Introduction: The Growing Importance of Digital Signature Security
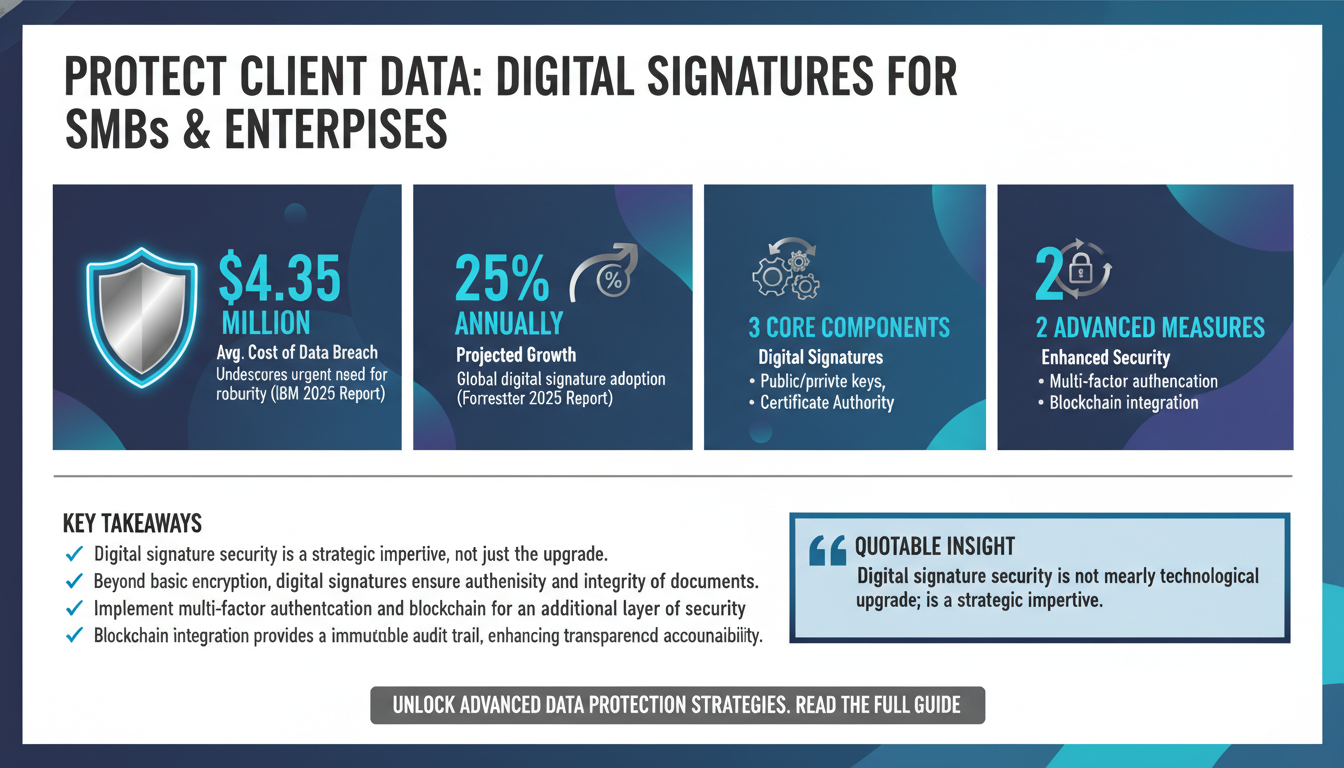
In an era where data breaches are increasingly common, safeguarding confidential client data has never been more critical. According to a 2025 IBM report, the average cost of a data breach reached a staggering $4.35 million last year, underscoring the urgent need for robust security measures. Digital signatures have emerged as a cornerstone of secure digital transactions, offering a legally binding method to authenticate documents while ensuring data integrity. This guide explores how small to medium-sized businesses (SMBs) and enterprises can leverage digital signatures to protect client data effectively. We'll delve into the technical aspects, best practices, and innovative solutions that can transform your digital security landscape.
Digital signature security is not merely a technological upgrade; it is a strategic imperative. With the rise of remote work and cloud-based operations, the need for secure e-signature solutions has become more pronounced. As businesses transition towards digital-first strategies, understanding how to implement and optimize these solutions is pivotal. In this comprehensive guide, we will dissect the nuances of digital signature technologies, explore industry-specific applications, and provide actionable insights to enhance your data protection framework.
For further insights on integrating digital signature solutions seamlessly, consider reading our detailed article on how small businesses can achieve seamless integration with digital signature solutions.
Understanding Digital Signatures: Beyond Basic Encryption
Digital signatures are often misunderstood as simple electronic scribbles. However, they are complex cryptographic protocols designed to ensure the authenticity and integrity of digital documents. A digital signature is created using a mathematical algorithm that generates a unique hash value for each document. This hash is encrypted with the sender's private key, creating a signature that is both unique and verifiable.
Key Components of Digital Signatures
To capitalize on these trends, businesses must understand the key components of digital signatures: the hash function, public and private keys, and the certificate authority (CA). The CA plays a crucial role in verifying the legitimacy of the keys, ensuring that the signatures cannot be forged. By integrating these elements into your security strategy, you can significantly enhance your organization's data protection capabilities.
Forrester's 2025 report highlights that the global adoption of digital signatures is set to increase by 25% annually, driven by advancements in encryption technologies and growing regulatory pressures. Organizations are moving beyond basic encryption to implement multi-factor authentication and blockchain technologies, which provide an additional layer of security.
Advanced Security Measures
Additional security measures such as multi-factor authentication and blockchain integration are becoming increasingly crucial. Multi-factor authentication adds layers of verification by requiring multiple forms of identification before a document can be signed. Blockchain, on the other hand, offers a decentralized ledger that ensures all transactions are transparent and immutable, further strengthening trust in the signed documents.

Pro Tip
Expert Insight: Consider integrating blockchain-based digital signatures into your existing systems. This integration not only enhances security but also builds an immutable audit trail, ensuring greater transparency and accountability in sensitive transactions.
For a more detailed exploration of how digital signatures can enhance workflow efficiency, refer to our guide on enhancing workflow efficiency with digital signatures.
Proprietary Framework: The Zignature Secure E-Signature Model (ZSEM)
Introducing the Zignature Secure E-Signature Model (ZSEM), a proprietary framework designed to optimize digital signature implementation while safeguarding client data. ZSEM is built around four core pillars: Compliance, Encryption, Verification, and Integration. By aligning these pillars, businesses can create a resilient digital signature infrastructure that withstands emerging threats.
Compliance and Regulatory Standards
Compliance: Ensuring adherence to industry-specific regulations such as GDPR, HIPAA, and eIDAS is critical. ZSEM incorporates automated compliance checks and audit trails, providing real-time alerts and reports to maintain regulatory standards. For instance, GDPR requires specific consent mechanisms for processing personal data, which ZSEM handles efficiently through automated workflows.
Encryption and Data Protection
Encryption: ZSEM leverages advanced encryption algorithms to protect data at rest and in transit. By utilizing 256-bit AES encryption, it ensures that documents are tamper-proof and accessible only to authorized users. This level of encryption is vital for industries dealing with sensitive data, such as financial services and healthcare, where breaches can lead to significant legal and financial repercussions.

Verification and User Authentication
Verification: Multi-factor authentication (MFA) and biometric verification are integral to ZSEM, adding an extra layer of security to the signature process. These measures help in verifying the identity of all parties involved, reducing the risk of unauthorized access. For instance, biometric verification like fingerprint or facial recognition can be used to confirm the signer's identity, enhancing trust and security.
Integration for Seamless Operations
Integration: Seamless integration with existing IT and document management systems is facilitated through APIs and SDKs, ensuring a smooth transition and minimal disruption to business processes. This is particularly beneficial for large enterprises with complex IT infrastructures that require custom solutions.
For insights on how digital signatures are essential for modern contract management, explore our article on modern contract management.
Contrarian Insights: Why Paper-Based Approaches Are Still Prevalent
Despite the clear advantages of digital signatures, a surprising number of organizations continue to rely on paper-based processes. According to a Gartner study, 37% of businesses still use paper for critical transactions. The reasons are multifaceted, ranging from resistance to change to misconceptions about digital signature security.
Myths and Misconceptions
One common myth is that digital signatures are not as legally binding as their ink-based counterparts. This is a fallacy; digital signatures are legally recognized in most jurisdictions worldwide. Another misconception is the perceived complexity of digital signature implementation. However, modern solutions are designed to be user-friendly, offering intuitive interfaces and robust support.
Cultural and Industry-Specific Barriers
Moreover, some industries have ingrained cultural preferences for paper documentation. Overcoming this inertia requires a strategic approach, emphasizing the long-term cost savings and environmental benefits of digital solutions. By educating stakeholders and demonstrating the tangible benefits of digital signatures, businesses can accelerate their transition to a paperless environment.

Expert Insight
Pro Tip: Conduct workshops and training sessions to familiarize staff with digital signature technologies. Highlight case studies where similar organizations have successfully transitioned to digital signatures, showcasing improved efficiency and compliance.
Explore how digital signatures can streamline healthcare compliance in our comprehensive guide on healthcare compliance.
Implementing Secure E-Signature Solutions: A Step-by-Step Guide
Implementing secure e-signature solutions involves more than just choosing the right software. It requires a strategic approach that considers the unique needs of your organization and its clients. Here, we outline a step-by-step process to ensure a successful deployment.
Step 1: Assess Your Needs
Step 1: Assess Your Needs - Begin by evaluating your current document management processes and identifying areas where digital signatures can add value. Consider the volume of documents, the level of security required, and any industry-specific compliance needs. This assessment will help you choose a solution that aligns with your operational goals.
Step 2: Choose the Right Solution
Step 2: Choose the Right Solution - Not all digital signature solutions are created equal. Evaluate vendors based on their security features, integration capabilities, and customer support. Look for solutions that offer end-to-end encryption and robust authentication measures. Ensure that the vendor can provide case studies or testimonials from similar businesses to validate their effectiveness.

Step 3: Train Your Team
Step 3: Train Your Team - Successful implementation hinges on user adoption. Provide comprehensive training to ensure all employees understand how to use the new system effectively. Offer resources such as FAQs, tutorials, and dedicated support channels. Consider appointing digital champions within departments to facilitate peer-to-peer learning and support.
Step 4: Monitor and Optimize
Step 4: Monitor and Optimize - Post-implementation, continuously monitor the system's performance and gather feedback from users. Use this data to make improvements and ensure the solution meets evolving business needs. Regularly review security protocols and update them in response to emerging threats or technological advancements.
For more detailed guidance on implementing digital signature solutions in healthcare, refer to our guide on improving patient data security.
Industry-Specific Applications: Tailoring Solutions for Maximum Impact
Different industries have unique requirements when it comes to digital signatures. Tailoring solutions to meet these specific needs can significantly enhance their effectiveness and adoption rate. Let's explore how digital signatures can be optimized for various sectors.
Legal Industry
Legal Industry: In legal settings, document integrity and authenticity are paramount. Digital signatures provide a tamper-proof seal that ensures documents remain unaltered. Additionally, audit trails and time-stamping features support compliance with legal standards. Legal firms can benefit from reduced paper costs and faster turnaround times for document processing.
Real Estate
Real Estate: For real estate professionals, speed and efficiency are critical. Digital signatures enable faster transaction closures and reduce the need for in-person meetings. Features such as remote signing and mobile access further enhance convenience. These benefits are essential in a competitive market where time is of the essence.
BCG's report on digital transformation in real estate highlights the growing adoption of digital signatures in the industry, citing a 40% increase in usage over the past two years.
Healthcare
Healthcare: Patient data security is a top priority in healthcare. Digital signatures ensure that sensitive information is protected while maintaining compliance with regulations like HIPAA. They also facilitate efficient document management, reducing administrative burdens. By minimizing paper use, healthcare providers can focus more on patient care and less on paperwork.
Expert Insight
Pro Tip: Customize your digital signature solution to align with industry-specific compliance requirements. This approach not only ensures legal adherence but also enhances client confidence in your security measures.
For a detailed exploration of how digital signatures can transform compliance in mergers and acquisitions, visit our article on M&A transactions.
Overcoming Common Pitfalls: Ensuring a Smooth Transition
Transitioning to digital signatures is not without its challenges. Understanding common pitfalls and how to overcome them is crucial for a successful implementation. Here are some key considerations:
Resistance to Change
Resistance to Change: Employees accustomed to traditional methods may resist adopting new technology. To mitigate this, involve them in the decision-making process and provide clear communication about the benefits and ease of use of digital signatures. Highlighting success stories from similar companies can also help ease apprehensions.
Security Concerns
Security Concerns: Some organizations fear that digital signatures may compromise security. However, when implemented correctly, they offer superior protection compared to paper-based methods. Utilize encryption and multi-factor authentication to address these concerns. Regular security audits and updates can further reassure stakeholders of the system's integrity.
Accenture's insights on digital transformation emphasize the importance of addressing security concerns to drive user adoption.
Integration Issues
Integration Issues: Integrating digital signature solutions with existing systems can be a technical challenge. Partner with vendors who offer strong API support and customization options to ensure seamless integration. Testing the solution in a controlled environment before full-scale deployment can identify potential issues early on.
Pro Tip
Expert Insight: Continuously engage with your vendor for updates and support. A proactive vendor can provide valuable insights into emerging trends and potential enhancements, ensuring your solution remains state-of-the-art.
For insights on reducing the environmental impact of digital signatures, explore our guide on environmental benefits.
Future Trends: The Evolution of Digital Signature Technologies
The future of digital signature technologies is promising, with continuous innovations transforming the landscape. Emerging trends include the integration of artificial intelligence, blockchain technology, and enhanced mobile capabilities.
Artificial Intelligence
Artificial Intelligence: AI is being used to improve the accuracy and efficiency of digital signature processes. Machine learning algorithms can detect anomalies and prevent fraudulent activities, enhancing overall security. AI can also streamline the user experience by automating routine tasks and providing predictive insights.
Blockchain
Blockchain: Blockchain offers a decentralized and immutable ledger for digital signatures, ensuring transparency and traceability. This technology is particularly valuable in industries requiring high levels of data integrity and auditability. As blockchain becomes more mainstream, its integration with digital signatures will likely become a standard practice.
Gartner's research on blockchain applications projects a 60% increase in its use for digital signatures by 2028, driven by its security and transparency benefits.
Mobile Capabilities
Mobile Capabilities: With the rise of remote work, mobile-friendly digital signature solutions are becoming essential. Enhanced mobile apps offer the flexibility to sign documents anytime, anywhere, without compromising security. This feature is particularly useful for businesses with a mobile workforce or those that operate in multiple time zones.
Expert Insight
Pro Tip: Stay informed about emerging technologies and consider pilot programs to test new features. Engaging with tech forums and industry conferences can provide early insights into innovations that could give your business a competitive edge.
To explore how blockchain is revolutionizing document authentication, refer to our article on the future of secure digital signatures.
FAQs: Common Questions About Digital Signature Security
Q1: Are digital signatures legally binding?
Yes, digital signatures are legally binding in most jurisdictions worldwide, provided they meet specific criteria for authenticity and integrity. Various laws, such as the eIDAS Regulation in the EU and the ESIGN Act in the US, recognize their legality.
Q2: How secure are digital signatures compared to traditional methods?
Digital signatures are more secure than traditional methods due to advanced encryption and authentication measures. They provide a tamper-proof seal and offer an audit trail to track document changes.
ThoughtWorks' insights provide an in-depth comparison of digital and traditional signature security.
Q3: What industries benefit most from digital signatures?
Industries such as legal, healthcare, finance, and real estate benefit significantly from digital signatures due to their need for document integrity, compliance, and efficiency.
Q4: Can digital signatures be used on mobile devices?
Yes, most digital signature solutions offer mobile-friendly platforms, allowing users to sign documents from smartphones and tablets securely.
Additional Resources
For a deeper dive into how digital signatures enhance data security in cross-border transactions, check out our article on cross-border data security.
For more information on the legal framework surrounding digital signatures, our guide on legal frameworks for digital signatures provides an extensive overview.
Conclusion: Embracing the Future of Secure Digital Transactions
As businesses continue to navigate the complexities of the digital age, safeguarding confidential client data with digital signatures becomes not just a necessity, but a strategic advantage. By embracing cutting-edge technologies and best practices, organizations can ensure the integrity and security of their digital transactions.
Implementing secure e-signature solutions requires a multifaceted approach that includes choosing the right technology, training users, and continuously optimizing systems for better performance. As we look to the future, innovations such as AI and blockchain will further enhance the capabilities of digital signatures, offering unprecedented levels of security and efficiency.
As you implement these strategies, consider complementing your efforts with tools like Apparatuz, which specializes in workflow automation, and Schedly, for scheduling and appointment management. Together, these approaches create a comprehensive solution for your business needs.
For ongoing support and resources, explore our resources section, where you'll find valuable insights and tools to enhance your digital signature strategy.
Ultimately, the shift towards secure digital transactions is not merely a trend but a fundamental evolution in how businesses operate. By staying informed and adaptable, your organization can not only protect its data but also gain a competitive advantage in an increasingly digital marketplace.