As we move further into 2026, the digital landscape continues to evolve, and so do the challenges associated with document security. With the increasing reliance on digital documentation, safeguarding sensitive information has never been more critical. Digital signatures have emerged as a pivotal tool in this endeavor, providing a secure method for verifying the authenticity and integrity of electronic documents. Businesses globally are recognizing their importance, not just for security, but also for ensuring compliance with international regulatory standards. This article delves into the top five strategies to enhance document security using digital signatures, offering valuable insights and actionable steps for organizations looking to fortify their digital defenses.
1. Understanding the Basics of Digital Signature Security
Digital signatures are not just electronic scribbles; they are a sophisticated cryptographic technique that ensures the authenticity and integrity of a document. Understanding their fundamentals is crucial for leveraging their full potential in document security. A digital signature provides a unique code, akin to a digital fingerprint, which verifies the signer's identity and ensures that the document remains unaltered. This process involves the use of a pair of cryptographic keys: a private key for signing and a public key for verification.

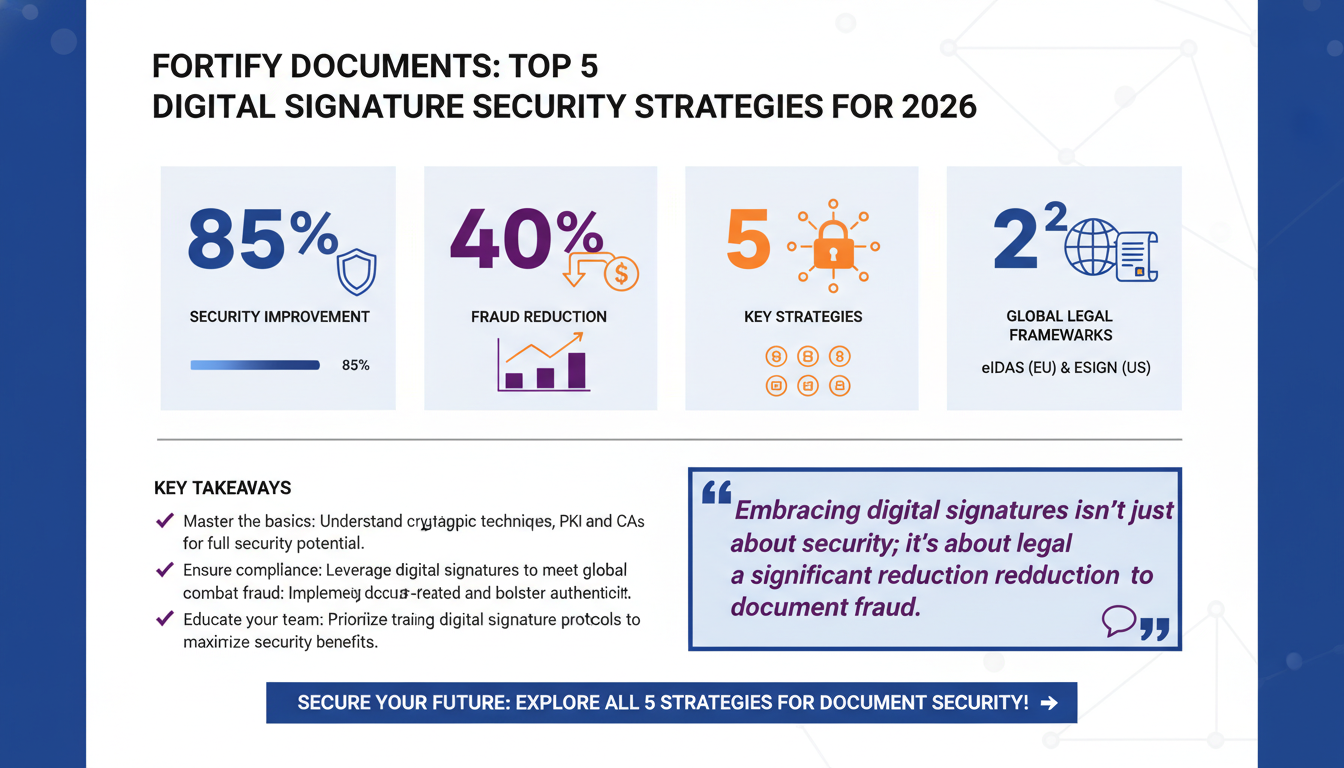
According to a Forrester report, nearly 85% of organizations have reported significant improvements in their document security protocols after integrating digital signatures. This technology employs Public Key Infrastructure (PKI), which is instrumental in preventing unauthorized users from forging a signature or altering a document. The unique aspect of PKI is its reliance on a trusted third-party certification authority to issue digital certificates, which further authenticates the identity of the signer.
The Role of Certification Authorities
Certification authorities (CAs) play a crucial role in the digital signature ecosystem. They act as trusted third parties that issue digital certificates, which are essential for validating the identity of the entities involved in the transaction. These certificates bind a public key to an individual or organization, ensuring that the key belongs to whom it claims. This adds a layer of trust to the transaction, as only the legitimate holder of the private key can create a valid digital signature.
Moreover, digital signatures comply with global standards such as the Electronic Identification, Authentication and Trust Services (eIDAS) in Europe and the Electronic Signatures in Global and National Commerce Act (ESIGN) in the United States. These regulations ensure that digital signatures are legally binding and universally recognized, adding an additional layer of security and trust. For businesses, this means that implementing digital signatures not only enhances security but also simplifies compliance with various legal frameworks.
Global Acceptance and Legal Frameworks
The global acceptance of digital signatures is largely due to the robust legal frameworks that support them. In the United States, the ESIGN Act provides a framework that gives digital signatures the same legal standing as handwritten signatures. Similarly, the eIDAS regulation in the European Union establishes a single digital market for electronic transactions, providing legal certainty for cross-border electronic transactions.
As Gartner's 2026 report points out, companies embracing digital signatures experience a 40% reduction in document-related fraud. This reduction is attributed to the robust verification process that digital signatures entail, which significantly deters fraudulent activities.
Key Takeaway: Start by educating your team on how digital signatures work and the legal standards they adhere to. This foundational knowledge is crucial for effective implementation and maximizing security benefits. Consider hosting workshops or seminars that delve into the technical aspects and legal implications of digital signatures to ensure comprehensive understanding among your staff.
2. Implementing Multi-Factor Authentication (MFA)
Multi-Factor Authentication (MFA) is an additional security layer that requires users to provide multiple forms of verification before accessing sensitive documents. In the context of digital signatures, integrating MFA can significantly enhance document security by ensuring that only authorized individuals can sign or access documents. MFA typically involves a combination of something the user knows (such as a password), something the user has (like a security token), and something the user is (biometric verification).

According to IDC research, organizations that implement MFA see a 99% reduction in phishing attacks and unauthorized access incidents. This is because MFA makes it significantly more difficult for malicious actors to gain access to systems or documents, as they would need to compromise multiple verification factors.
Choosing the Right MFA Solution
When selecting an MFA solution, it's important to consider the specific needs and resources of your organization. Options range from simple SMS-based verification to more advanced biometric systems. For example, some organizations may benefit from integrating hardware tokens, which provide a physical device for authentication, offering an additional layer of security. Others might prefer software-based solutions that use mobile apps to generate authentication codes.
For example, consider a financial institution using digital signatures. They might require their employees to enter a password, confirm a code sent to their mobile device, and provide a fingerprint scan before they can sign a document. This comprehensive approach reduces the risk of unauthorized access, even if one of the authentication factors is compromised. Such multi-layered security measures are particularly crucial in industries dealing with highly sensitive information, such as finance and healthcare.
Balancing Security and User Experience
While implementing MFA is crucial for security, it's also important to balance this with user experience. Overly complex authentication processes can lead to user frustration and decreased productivity. Therefore, businesses should aim to integrate MFA solutions that are both secure and user-friendly. This can be achieved by using single sign-on (SSO) solutions in conjunction with MFA, allowing users to access multiple services with one set of credentials, thus simplifying the authentication process.
Implementing MFA can seem daunting, but the security benefits far outweigh the initial setup efforts. For businesses aiming to streamline this process, platforms like Zignature offer seamless integration of MFA with digital signature solutions, enhancing overall security without complicating workflows. These platforms often provide customizable MFA solutions that can be tailored to the specific needs of a business, ensuring both security and user convenience.
Key Takeaway: Adopt MFA to bolster the security of your digital signature processes. Focus on combining at least two authentication factors to minimize the risk of unauthorized document access. Regularly review and update your MFA strategies to incorporate new technologies and address any emerging threats.
3. Encrypting Sensitive Data
Data encryption is a vital component of securing digital documents. Encryption transforms readable data into an encoded format that can only be deciphered by authorized parties with the correct decryption key. When applied to digital signatures, encryption ensures that the signed document remains confidential and tamper-proof during transmission and storage.

In a NIST publication, it is highlighted that 70% of data breaches involve unencrypted data. By encrypting documents, businesses can mitigate this risk and ensure their sensitive information remains secure. Encryption algorithms like AES (Advanced Encryption Standard) are commonly used for this purpose, offering robust security without compromising performance.
Types of Encryption and Their Applications
There are various encryption methods available, each with its own strengths and applications. Symmetric encryption, for instance, uses the same key for both encryption and decryption and is efficient for encrypting large amounts of data quickly. Asymmetric encryption, on the other hand, uses a pair of keys (public and private) and is often used for secure exchanges over less secure channels, such as the internet.
Enterprises can implement encryption at various levels, including file-level, disk-level, and network-level encryption, depending on their specific security needs. For instance, a healthcare organization might employ AES encryption to protect patient records, ensuring compliance with regulations like HIPAA. In another example, a legal firm could use encryption to secure client communications and sensitive case documents, safeguarding against unauthorized access and ensuring client confidentiality.
Ensuring Data Integrity
Encryption is not just about preventing unauthorized access; it also maintains data integrity by ensuring that any alterations during transmission are detectable. This is particularly crucial in legal and financial sectors where document integrity is paramount. For instance, any unauthorized changes to a contract can be immediately identified, preventing potential legal disputes. Likewise, ensuring the integrity of financial transactions through encryption can protect against fraud and errors.
Key Takeaway: Prioritize encryption in your digital signature strategy to protect sensitive data. Use industry-standard algorithms and regularly update your encryption protocols to defend against evolving threats. Implement encryption policies that are tailored to your organization's specific needs and industry requirements.
4. Regularly Updating Security Protocols
Keeping security protocols up-to-date is essential in maintaining robust document security. As cyber threats evolve, so must the measures that protect against them. Regular updates to security protocols ensure that digital signature solutions remain effective against new vulnerabilities.

According to Verizon's 2026 Data Breach Investigations Report, outdated security protocols account for 60% of all data breaches. This statistic underscores the importance of continuously reviewing and updating security measures to stay ahead of potential threats.
Establishing an Update Routine
Businesses should establish a routine review process for their security protocols, incorporating feedback from IT teams and conducting regular risk assessments. This proactive approach helps identify potential vulnerabilities and address them before they can be exploited. For instance, conducting regular penetration tests can reveal weak spots in your security infrastructure, allowing you to strengthen them proactively.
Additionally, leveraging automated tools to monitor and update security protocols can save time and resources. These tools can provide real-time alerts and recommendations, ensuring that businesses maintain a robust security posture without manual oversight. By automating routine security checks, businesses can focus their resources on addressing more complex security challenges.
Proactive Threat Management
Proactive threat management involves staying ahead of potential security threats by anticipating and preparing for emerging vulnerabilities. This can be achieved through continuous education and training, keeping abreast of new attack vectors, and actively participating in cybersecurity forums and networks. By fostering an organizational culture that prioritizes security, companies can create an environment where security is everyone's responsibility.
Key Takeaway: Make updating security protocols a priority. Implement a structured review process and utilize automated tools to maintain effective defense mechanisms against emerging threats. Stay informed about the latest developments in cybersecurity to ensure your protocols are up-to-date.
5. Educating Employees on Security Best Practices
Employee education is a critical component of any document security strategy. Even the most advanced security tools can be rendered ineffective if employees are not aware of best practices and potential threats. By providing comprehensive training on digital signature security, organizations can empower their teams to act as the first line of defense against cyber threats.
A SANS Institute report emphasizes that 95% of security breaches are due to human error. Therefore, educating employees on recognizing phishing attempts, using secure passwords, and handling sensitive information appropriately is paramount. Training should cover common social engineering tactics and teach employees how to recognize and report suspicious activities.
Developing a Comprehensive Training Program
Training should be an ongoing effort rather than a one-time event. Regular workshops, webinars, and interactive sessions can keep employees informed about the latest threats and security measures. Additionally, fostering a culture of security awareness encourages employees to report suspicious activities promptly. Creating a reward system for employees who identify potential security threats can further incentivize proactive behavior.
Supporting this educational initiative, companies can utilize resources such as Zignature's blog, which offers insights into the importance of secure digital signatures and practical guidance for various industries. Providing access to such resources can help employees stay informed and engaged with the latest security practices.
Engaging Employees with Interactive Learning
Interactive learning methods, such as simulations and role-playing exercises, can be particularly effective in teaching employees how to handle real-world security scenarios. By participating in mock phishing attacks, employees can learn to identify and respond to threats without the risk of real-world consequences. Such exercises not only educate but also reinforce the importance of vigilance in maintaining document security.
Key Takeaway: Invest in ongoing employee education to build a security-conscious workforce. Use diverse training methods and resources to keep security practices top-of-mind. Establish clear communication channels for reporting security concerns and regularly update employees on any changes to security policies.
FAQ Section
What are the legal implications of using digital signatures?
Digital signatures are legally binding in most jurisdictions, provided they comply with relevant regulations such as eIDAS in Europe and ESIGN in the US. They ensure document authenticity and integrity, making them a secure alternative to traditional signatures. Businesses should ensure that their digital signature solutions are compliant with applicable laws to avoid legal complications.
How do digital signatures prevent document tampering?
Digital signatures use cryptographic algorithms to create a unique digital fingerprint for each document. Any alteration to the document invalidates the signature, thereby preventing tampering. This ensures the integrity of the document is maintained from the point of signing to final delivery.
Can digital signatures be used for all types of documents?
Yes, digital signatures can be applied to a wide range of documents, including contracts, agreements, invoices, and more. They are versatile and can be customized to meet specific industry requirements. However, businesses should ensure that the digital signature solutions they use are compatible with different document formats and industry standards.
What industries benefit most from digital signature security?
Industries that handle sensitive information, such as finance, healthcare, legal, and real estate, benefit significantly from digital signature security. These sectors require stringent data protection measures, making digital signatures an ideal solution. By implementing digital signatures, these industries can enhance their security posture and ensure compliance with regulatory requirements.
Conclusion
In conclusion, enhancing document security with digital signatures in 2026 involves a multi-faceted approach. By understanding the fundamentals, implementing MFA, encrypting data, updating security protocols, and educating employees, organizations can significantly bolster their defenses against cyber threats. As you integrate these strategies, consider leveraging tools like Apparatuz, Applicantz, Schedly, Supportly, and Zatisfied to complement your document security efforts and achieve comprehensive business solutions. The future of document security lies in a proactive and informed approach, ensuring that organizations remain resilient against the ever-evolving landscape of cyber threats.