In today’s digital-first world, intellectual property (IP) has become one of the most critical assets for businesses of all sizes. Whether it’s a groundbreaking patent, a recognizable trademark, or a proprietary algorithm, IP is often the foundation upon which companies build their competitive edge. However, as valuable as these assets are, they are equally vulnerable to theft, unauthorized access, and misuse, especially in an era where cyber threats are escalating, and globalized business operations make IP protection even more complex.
Traditional methods of safeguarding IP, such as physical document storage and manual agreements, are increasingly inadequate in combating the sophisticated threats businesses face today. The need for a robust, secure, and legally enforceable solution has never been greater. Enter digital signatures—a transformative technology that combines cryptographic security with legal validity to protect and manage intellectual property effectively.
This comprehensive guide delves into the critical role digital signatures play in securing intellectual property. By exploring their technical capabilities, legal implications, and practical applications, this guide will empower small-to-medium-sized businesses (SMBs) and enterprises to integrate digital signatures into their IP management strategies seamlessly. From understanding the nuances of digital signatures to actionable steps for implementation, this article covers it all.
Understanding Intellectual Property in the Digital Age
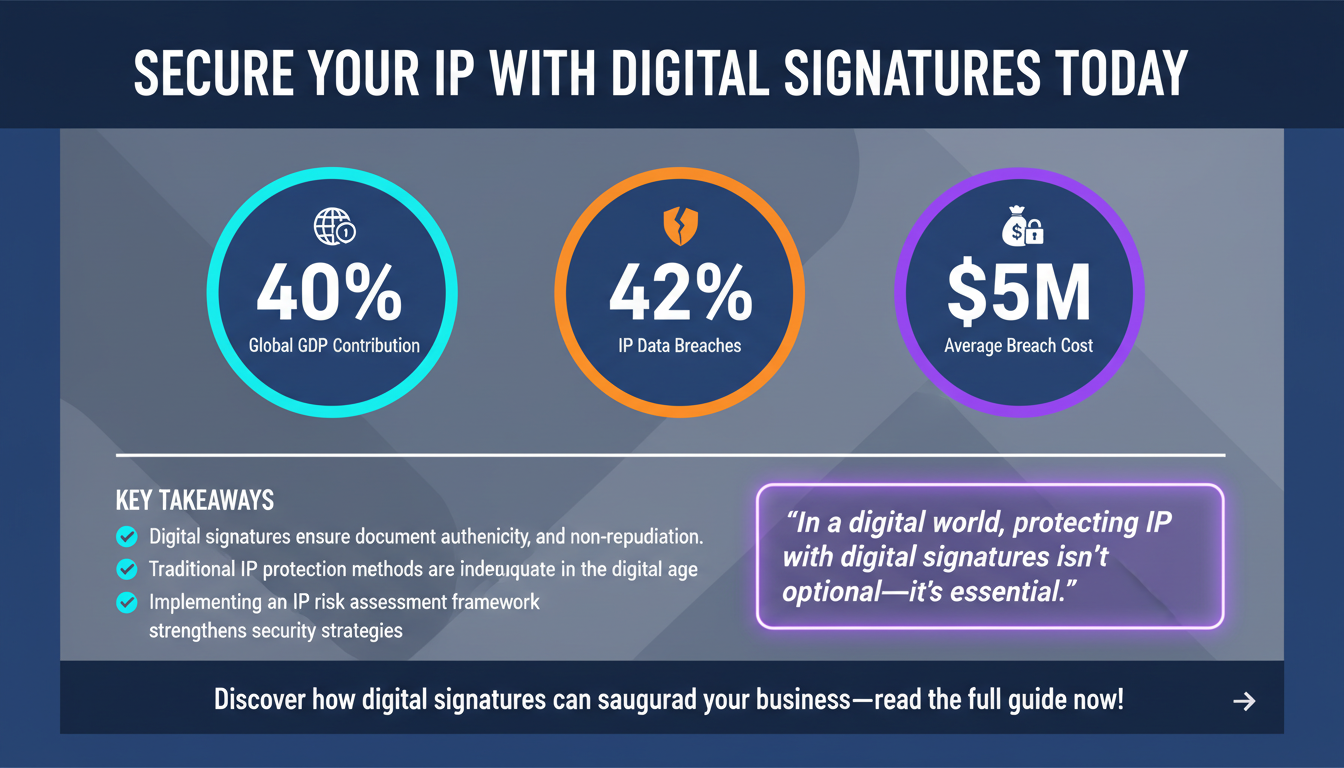
Intellectual property refers to intangible assets that derive their value from innovation, creativity, and proprietary knowledge. These assets include patents, copyrights, trademarks, trade secrets, and even certain business processes. According to the World Intellectual Property Organization (WIPO), IP-intensive industries contribute over 40% of the global GDP and employ millions of people worldwide. This underscores the economic significance of IP and the need to protect it effectively.

The Challenges of Protecting IP in the Digital Era
However, the digital transformation sweeping across industries has brought new challenges to IP protection. Cybersecurity threats such as data breaches, phishing attacks, and insider leaks pose significant risks. For example, a 2025 report from McKinsey revealed that 42% of organizations experienced IP-related data breaches in the past year, with the average cost per incident reaching $5 million. These numbers highlight the urgency of adopting advanced security measures.
Moreover, the interconnected nature of modern business operations, such as cross-border collaborations and cloud-based work environments, increases the likelihood of unauthorized access or accidental disclosure of sensitive IP. The reliance on traditional methods of protection—like physical contracts and wet signatures—has proven inadequate in mitigating these risks, especially when dealing with global transactions.
Pro Tip: Adopt an IP Risk Assessment Framework
Businesses can benefit from implementing an IP risk assessment framework to identify vulnerabilities within their digital and physical workflows. Tools like the NIST Cybersecurity Framework provide a structured approach to assessing risks and strengthening security measures, including the integration of digital signatures for document protection.
This is where digital signatures step in. By ensuring the authenticity, integrity, and non-repudiation of digital documents, they provide a secure framework for safeguarding IP assets. For example, a company can use digital signatures to time-stamp patent applications, authenticate licensing agreements, or secure non-disclosure agreements (NDAs). Let’s explore how digital signatures work and why they are uniquely suited to address the challenges of IP protection in the digital age.
What Are Digital Signatures and How Do They Work?
Digital signatures are a type of electronic signature that uses cryptographic algorithms to verify the authenticity and integrity of digital documents. Unlike simple electronic signatures, which can be as basic as a scanned image of a handwritten signature, digital signatures rely on public key infrastructure (PKI) to create a highly secure and verifiable digital “fingerprint.”

Step-by-Step Breakdown of Digital Signature Functionality
Here’s a detailed step-by-step breakdown of how digital signatures work:
- Document Hashing: The content of the document is processed through a mathematical algorithm to generate a unique hash value. This hash acts as a digital representation of the document’s contents, ensuring that even a minor change to the document would generate a completely different hash.
- Encryption: The generated hash value is encrypted using the sender’s private key, creating the digital signature. Since private keys are unique and confidential, this ensures the signature’s authenticity, as only the sender can encrypt the hash with their private key.
- Verification: When the document is received, the recipient uses the sender’s public key to decrypt the digital signature and retrieve the original hash value. The recipient then generates a new hash from the document and compares it with the decrypted hash. If the two match, the document is verified as authentic and untampered.
Key Advantages for IP Protection
This process ensures two critical outcomes:
- Authenticity: The document is verified to have originated from the claimed sender, which is essential for proving ownership of intellectual property.
- Integrity: The document has not been altered since it was signed, providing a tamper-proof record of agreements or filings.
For intellectual property, these features are indispensable. Whether it’s proving ownership of a patent, ensuring the validity of a licensing agreement, or maintaining the confidentiality of trade secrets, digital signatures offer a robust, tamper-proof solution.
Real-World Application Example
Consider a scenario where a tech startup develops a proprietary algorithm. To protect its IP, the company uses digital signatures to time-stamp the algorithm’s codebase and secure contracts with developers and clients. By doing so, the startup ensures that its IP is not only protected from unauthorized access but is also legally verifiable in case of disputes.
Expert Insight: Why PKI Matters
According to cybersecurity experts, leveraging public key infrastructure (PKI) is a game changer for businesses dealing with intellectual property. PKI ensures a layered security model where private and public keys work in tandem, providing encryption, authentication, and integrity for IP-sensitive documents. Gartner predicts that by 2027, over 80% of enterprise IP transactions will incorporate PKI-based digital signatures.
Legal and Regulatory Implications of Digital Signatures
One of the most significant advantages of digital signatures is their legal validity. In many jurisdictions, digital signatures are recognized as legally binding under comprehensive regulatory frameworks. These include:

- eIDAS Regulation (EU): The Electronic Identification, Authentication, and Trust Services regulation categorizes digital signatures into three levels—simple, advanced, and qualified electronic signatures. Qualified electronic signatures offer the highest level of legal recognition in the EU.
- ESIGN Act (US): The Electronic Signatures in Global and National Commerce Act grants electronic signatures, including digital signatures, the same legal standing as handwritten signatures in the United States.
- IT Act (India): In India, the Information Technology Act provides legal recognition for digital signatures, making them admissible in court as evidence.
Compliance and Risk Mitigation
These regulations not only establish the legal credibility of digital signatures but also facilitate their use in sensitive IP-related transactions. For instance, companies in the European Union can leverage qualified electronic signatures to file patents or secure trade agreements with the assurance of legal enforceability.
Another critical aspect is compliance with data protection laws like the General Data Protection Regulation (GDPR). By ensuring secure and auditable documentation, digital signatures help businesses demonstrate accountability and transparency in handling sensitive IP, reducing the risk of regulatory penalties. Under GDPR, non-compliance can result in fines of up to 4% of a company’s global annual turnover, making secure IP management a business imperative.
Comparison Table: Digital Signatures vs Traditional Signatures
| Aspect | Digital Signatures | Traditional Signatures |
|---|---|---|
| Security | Encrypted and tamper-proof | Vulnerable to forgery |
| Authenticity | Cryptographically verifiable | Requires physical verification |
| Legal Recognition | Globally recognized under regulations like eIDAS and ESIGN | Limited to specific jurisdictions |
| Efficiency | Instant and scalable | Time-consuming |
Pro Tip: Localize Compliance Efforts
For multinational businesses, it’s essential to understand the specific digital signature regulations in each operating jurisdiction. Partnering with legal experts or using a global digital signature platform can streamline compliance efforts.
How Digital Signatures Protect Different Types of Intellectual Property
Intellectual property spans a diverse range of assets, each requiring specialized protection measures. Digital signatures provide versatile solutions across the spectrum of IP categories:

1. Patents
Patent applications and filings often involve multiple stakeholders, including inventors, attorneys, and patent offices. Digital signatures ensure that these documents are tamper-proof and time-stamped, providing irrefutable evidence of originality and ownership. For instance, a pharmaceutical company filing a patent for a new drug can use digital signatures to authenticate its application, reducing the risk of disputes over ownership.
2. Trademarks
Trademarks are critical for brand identity, and their registration often involves legally binding agreements. Digital signatures streamline this process by enabling secure authentication, reducing paperwork delays, and ensuring compliance with regulatory requirements.
3. Copyrights
For creative works like music, films, and software, digital signatures allow creators to securely share drafts and agreements while maintaining proof of authorship and ownership. For example, a software developer can use digital signatures to protect source code from unauthorized modifications or theft.
4. Trade Secrets
Protecting trade secrets requires stringent confidentiality measures. Digital signatures facilitate secure NDAs and data-sharing agreements, ensuring that sensitive information remains protected. For instance, a manufacturing company can use digital signatures to secure contracts with suppliers, protecting proprietary production methods from leaks.
Proprietary Framework: The 5-Steps to Implementing Digital Signatures for IP Protection
To ensure the successful adoption of digital signatures, businesses should follow a structured implementation process. At Zignature, we recommend the “5-S Framework”:
- Strategize: Identify IP assets that require protection and map out workflows involving these assets.
- Secure: Choose a trusted digital signature provider that meets your legal and operational needs.
- Standardize: Develop internal guidelines for using digital signatures in IP-related processes, such as patent filings and NDAs.
- Streamline: Integrate digital signatures into existing tools and platforms for seamless adoption.
- Sustain: Regularly audit and update your digital signature practices to address evolving security and compliance requirements.
Each step ensures alignment with industry best practices, fostering a robust approach to IP protection.
Conclusion: Embracing Digital Signatures as a Strategic Asset
In a world where intellectual property is both a cornerstone of innovation and a target for cyber threats, digital signatures provide an indispensable tool for businesses aiming to protect their assets. By ensuring the authenticity, integrity, and legal validity of IP-related documents, digital signatures not only safeguard sensitive information but also streamline operations and enhance compliance.
For SMBs and enterprises alike, adopting digital signatures is not just a technical upgrade—it’s a strategic imperative. Whether you’re securing a patent, protecting a trade secret, or negotiating a licensing agreement, digital signatures offer a scalable, efficient, and legally robust solution. At Zignature, we are dedicated to helping businesses navigate this transformation with secure, user-friendly, and compliant digital signature solutions. Learn more about our platform features and protect your intellectual property today.
To further enhance your digital workflows, explore our sister platforms: Apparatuz for workflow automation, Applicantz for recruitment management, Schedly for scheduling and appointments, Supportly for customer support, and Zatisfied for feedback management. Together, these tools create a comprehensive ecosystem that complements your digital signature strategy.