In a world where data breaches, compliance risks, and client trust are critical challenges for businesses, securely managing sensitive client data has never been more important. Digital signatures have emerged as a cornerstone technology for ensuring data security, enabling businesses to maintain compliance, streamline workflows, and protect their reputation. In 2026, the landscape of digital signature solutions has evolved significantly, offering unparalleled security features and functionalities. This article explores the top strategies for managing sensitive client data securely using digital signatures, with actionable insights, expert tips, and industry trends.
1. Leverage Advanced Encryption Algorithms
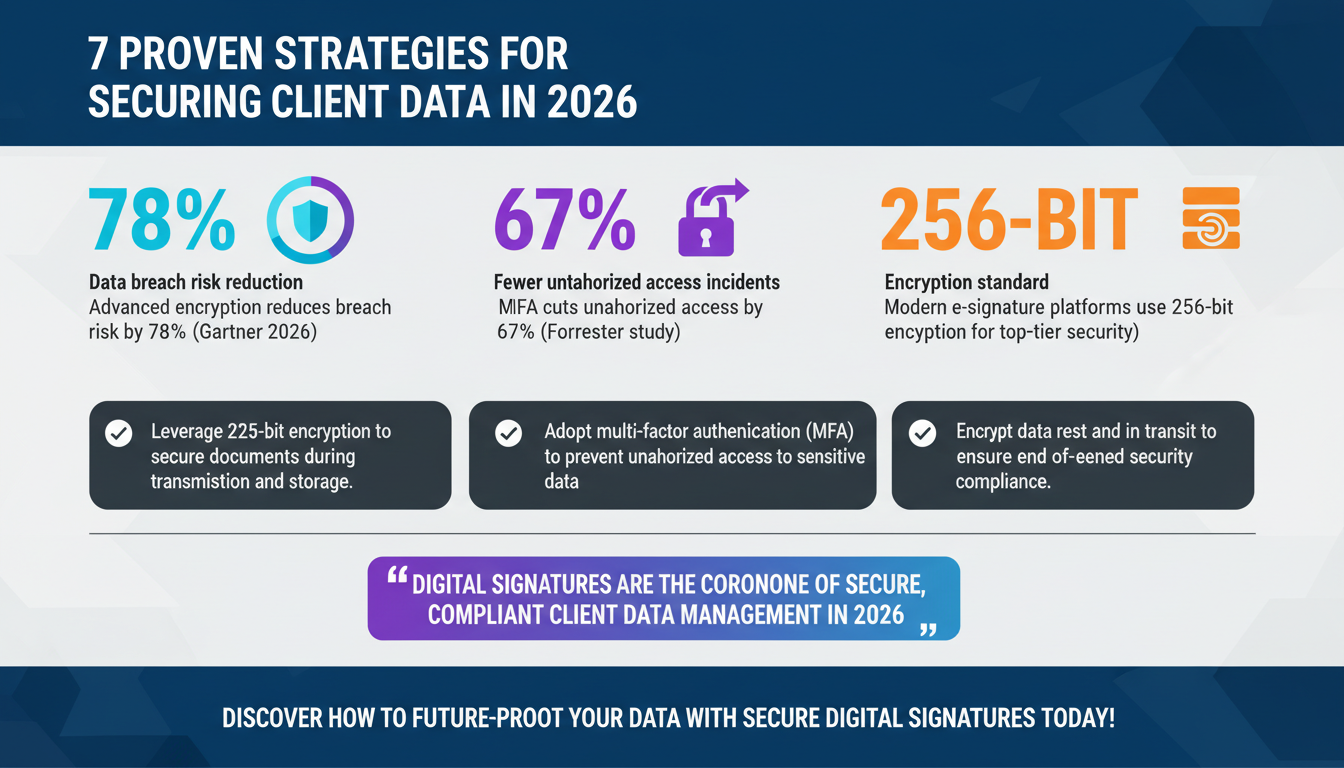
Encryption is the backbone of secure digital signatures. By leveraging advanced encryption algorithms, businesses can ensure that sensitive client data remains protected during transmission and storage. Modern e-signature platforms use 256-bit encryption, which is nearly impossible to crack with current computing capabilities. This level of encryption safeguards the integrity and confidentiality of documents and ensures compliance with rigorous data protection regulations like GDPR and HIPAA.
For example, encryption ensures that a signed contract cannot be intercepted or altered by unauthorized parties. Companies like Zignature have adopted encryption standards that exceed industry norms, enabling clients to securely exchange sensitive information across global networks.
Key benefits of advanced encryption include:
- Protecting data from unauthorized access during transmission
- Ensuring document integrity and authenticity
- Complying with international data security standards
Gartner’s 2026 report highlights the increasing adoption of advanced encryption in e-signature platforms, citing its role in reducing data breach risks by 78%.

2. Implement Multi-Factor Authentication (MFA)
Multi-factor authentication (MFA) has become a non-negotiable security measure in 2026. By requiring users to verify their identity through multiple channels—such as a password, biometric scan, or a one-time PIN—MFA adds an extra layer of protection to sensitive digital transactions. This approach prevents unauthorized access even if an attacker gains access to a user's credentials.
For instance, legal teams managing high-value contracts can use MFA to ensure only authorized personnel can access and sign documents. This reduces the risk of fraud and enhances compliance with regulatory frameworks.
According to Forrester’s study on authentication security, organizations that implement MFA experience a 67% reduction in unauthorized access incidents compared to those relying solely on passwords.
Steps to implement MFA securely:
- Choose an e-signature platform with integrated MFA capabilities
- Ensure compatibility with biometric authentication tools
- Train employees on MFA best practices

3. Encrypt Data at Rest and in Transit
Data encryption must extend beyond transmission; it should also secure data at rest. Sensitive client information stored in databases, cloud servers, and devices must be encrypted to prevent unauthorized access, theft, or exposure in the event of a breach. Leading digital signature platforms in 2026 employ end-to-end encryption to ensure data remains protected at every stage.
For example, Zignature’s platform encrypts documents both at rest and in transit, preventing vulnerabilities during storage or email exchanges. This dual-layer encryption ensures compliance with stringent industry regulations and reassures clients of the platform’s commitment to security.
IDC’s research reveals that organizations encrypting data in transit and at rest reduce data leak risks by 81%. This approach is essential for industries like healthcare, finance, and legal, where client data is highly sensitive.

4. Conduct Regular Security Audits
Regular security audits are vital for identifying vulnerabilities and reinforcing security measures. By proactively assessing risks in digital signature workflows, organizations can ensure compliance and prevent data breaches. Security audits evaluate encryption protocols, authentication methods, and access controls to ensure they meet evolving security standards.
For example, a financial institution managing sensitive loan agreements can benefit from quarterly security audits to ensure their digital signature processes align with regulations like PCI DSS.
Steps for effective security auditing:
- Engage third-party security experts to conduct penetration tests
- Use automated tools to monitor system vulnerabilities
- Document audit findings and implement recommendations
Accenture’s 2026 insights highlight that security audits reduce breach incidents by up to 92% for organizations using advanced e-signature technologies.
5. Ensure Compliance with Global Regulations
Compliance with global data protection regulations is a top priority for businesses in 2026. Digital signature platforms must adhere to laws like GDPR, HIPAA, and CCPA to ensure sensitive client data is handled securely and legally. Non-compliance can result in hefty penalties and damage to reputation.
For example, healthcare providers can use compliant e-signature platforms to securely manage patient consent forms while meeting HIPAA requirements. Similarly, multinational corporations must ensure compliance with cross-border data privacy laws.
PwC’s regulatory trends emphasize the need for businesses to adopt digital signature solutions that offer built-in compliance features, reducing regulatory risks by 85%.
6. Train Employees on Security Best Practices
Human error remains one of the leading causes of data breaches. Training employees on security best practices is essential for minimizing risks in digital signature workflows. Education on secure document handling, phishing prevention, and authentication protocols can ensure employees act as the first line of defense.
For instance, onboarding programs can include modules on recognizing fraudulent signature requests and securely sharing signed documents. Companies like Zignature provide regular training resources to help clients maintain robust security practices.
Harvard Business Review’s study found that organizations investing in employee security training reduce data breach incidents by 63%.
7. Use Blockchain Technology for Audit Trails
Blockchain technology has revolutionized how businesses manage audit trails for digital signatures. By providing immutable, transparent records of all signature actions, blockchain ensures accountability and prevents tampering. This technology is particularly useful for industries requiring high levels of documentation integrity, such as legal and finance.
For example, Zignature’s adoption of blockchain-based audit trails allows clients to track every action taken on a document—from signing to modifications—ensuring full transparency and confidence in the process.
Blockchain News reports that 76% of organizations using blockchain for audit trails experience improved compliance and reduced fraud risks.
FAQs
What are the key security features of digital signatures?
Key features include advanced encryption, multi-factor authentication, blockchain audit trails, and compliance with global regulations. These ensure data integrity, confidentiality, and legal validity.
How do digital signatures comply with GDPR?
Digital signature platforms comply with GDPR by encrypting data, offering audit trails, and ensuring user consent for data usage. They also provide data handling transparency.
Can digital signatures be used for cross-border transactions?
Yes, compliant digital signature solutions are designed to meet international regulations, making them suitable for cross-border agreements and transactions.
What industries benefit most from secure digital signatures?
Industries like healthcare, finance, legal, and real estate benefit significantly due to their need for secure, compliant handling of sensitive client data.
How do I choose the right digital signature platform?
Look for features like encryption, MFA, compliance capabilities, blockchain audit trails, and scalability. Platforms like Zignature are tailored for SMBs and enterprises alike.
Conclusion
Digital signatures have become indispensable for securely managing sensitive client data in 2026. By leveraging advanced encryption, MFA, blockchain technology, and compliance features, businesses can protect their clients’ information while optimizing workflows. As threats evolve, staying ahead with secure digital signature solutions is vital for maintaining trust and achieving operational excellence. Platforms like Zignature offer robust tools and expert support to help businesses adopt these strategies effectively.
Ready to transform your data security and workflows? Explore Zignature’s features or contact us today.
To further enhance your digital workflows, explore our sister platforms: Apparatuz for workflow automation, Applicantz for recruitment management, Schedly for scheduling and appointments, Supportly for customer support, and Zatisfied for feedback management. Together, these tools create a comprehensive ecosystem that complements your digital signature strategy.