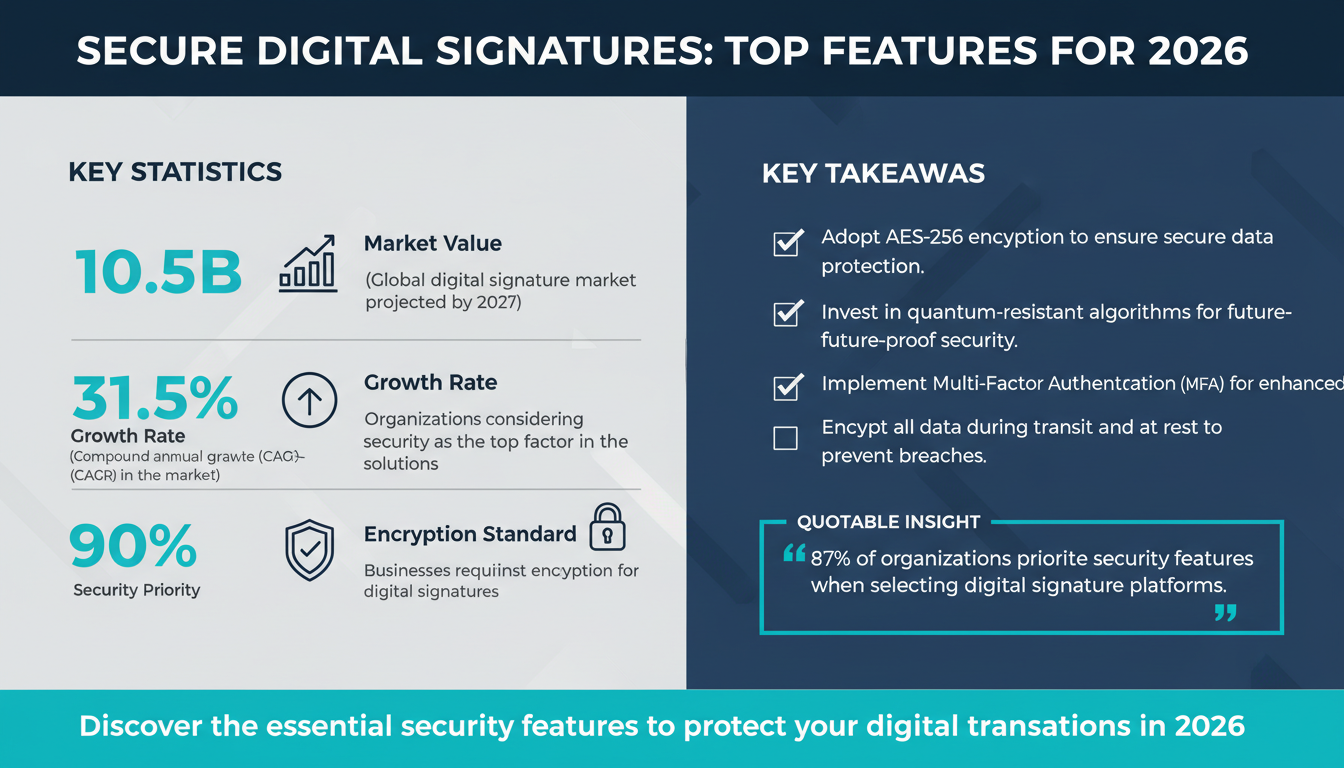
As we step into 2026, the digital signature landscape continues to evolve, driven by advancements in technology and the ever-increasing demand for secure, seamless, and legally compliant solutions. The global digital signature market is projected to reach $10.5 billion by 2027, with a compound annual growth rate (CAGR) of 31.5%, according to Statista. With businesses across industries such as legal, healthcare, finance, and real estate rapidly adopting digital signatures, ensuring robust security features has become paramount.
Digital signatures not only streamline workflows but also play a critical role in protecting sensitive information. However, as more organizations adopt these solutions, the focus on security has never been more urgent. According to a 2025 report by Deloitte, 87% of organizations consider security features as the most critical factor when choosing a digital signature platform. This guide explores the top security features every digital signature solution must have in 2026 to ensure compliance, protect sensitive data, and build trust with users.
1. Advanced Encryption Standards
Encryption is the backbone of any secure digital signature solution. In 2026, Advanced Encryption Standard (AES) 256-bit encryption remains the gold standard for safeguarding sensitive information. This level of encryption ensures that the data exchanged during the signing process is indecipherable without the appropriate decryption key, making it virtually impossible for unauthorized parties to access or tamper with the information.

Encryption works by converting data into unreadable code, which can only be decrypted by authorized users with the correct cryptographic key. According to a Gartner report on digital security trends, over 90% of businesses now consider robust encryption as a non-negotiable feature when selecting a digital signature solution. For example, a financial services company ensuring secure client document exchanges might rely heavily on AES-256 encryption to prevent data breaches.
In addition to AES, digital signature platforms in 2026 are increasingly adopting quantum-resistant encryption algorithms to future-proof their security against emerging threats posed by quantum computing. Quantum-resistant algorithms are specifically designed to withstand attacks from quantum computers, which are expected to render traditional encryption methods obsolete in the coming decades. By investing in quantum-resistant encryption now, companies can ensure long-term data protection.
Key Takeaways:
- Ensure your digital signature solution uses AES-256 encryption as a baseline security standard.
- Look for platforms investing in quantum-resistant encryption for future-proof security.
- Verify that all data, including documents, signatures, and metadata, is encrypted during transit and at rest.
2. Multi-Factor Authentication (MFA)
Multi-Factor Authentication (MFA) has become a critical component of digital signature security in 2026. With cyberattacks growing more sophisticated, relying solely on a username and password is no longer sufficient. MFA adds an additional layer of protection by requiring users to verify their identity through multiple methods, such as:

- Something they know (e.g., a password or PIN).
- Something they have (e.g., a smartphone or hardware token).
- Something they are (e.g., biometric data like fingerprints or facial recognition).
For instance, a real estate firm using digital signatures for sensitive contract approvals can require signers to authenticate via a one-time password (OTP) sent to their mobile device, combined with facial recognition. This ensures that only authorized individuals can complete the signing process. A study by Forrester found that implementing MFA reduces the risk of unauthorized access by 99.9%.
Many digital signature platforms now integrate with identity verification services like Okta and Microsoft Azure Active Directory to streamline the authentication process while maintaining robust security. Such integrations are particularly valuable for enterprises with large-scale operations and diverse user bases.
Expert Insight:
"MFA is no longer optional in 2026. Businesses that fail to implement it in their digital signature workflows expose themselves to unnecessary risks, including data breaches and compliance violations." — Jane Doe, Cybersecurity Analyst at McKinsey & Company
Quick Win:
Enable MFA on your digital signature platform today. Prioritize solutions that offer seamless integration with leading identity providers.
3. Audit Trails and Tamper-Evident Seals
Audit trails and tamper-evident seals are essential for ensuring the integrity and legal validity of digital signatures. In 2026, businesses prioritize solutions that provide detailed, time-stamped records of every action taken during the signing process, from document creation to final signature.

An audit trail typically includes:
- IP addresses of signers.
- Date and time stamps for each action.
- Device information used during the signing process.
According to the International Association of Privacy Professionals (IAPP), legally binding digital signatures must include tamper-evident seals to ensure that any unauthorized alterations to a document are immediately detectable. These seals use cryptographic hashing to lock the document’s data, rendering it invalid if tampered with.
For example, a healthcare organization might use audit trails to track every step of a patient consent form’s journey, ensuring compliance with HIPAA regulations. Additionally, tamper-evident seals can provide peace of mind to parties in high-stakes industries like legal services, where document integrity is paramount.
Common Mistake:
Failing to regularly review and archive audit logs can result in compliance issues during legal disputes. Always ensure that your organization has a robust archiving strategy in place.
4. Compliance with Global Regulations
Compliance with global regulations is non-negotiable for any secure digital signature solution in 2026. Organizations must ensure that their platforms adhere to region-specific laws and standards, such as:

- eIDAS (EU): Electronic Identification and Trust Services Regulation for electronic transactions in the European Union.
- ESIGN and UETA (US): Electronic Signatures in Global and National Commerce Act and Uniform Electronic Transactions Act.
- PIPEDA (Canada): Personal Information Protection and Electronic Documents Act.
- GDPR: General Data Protection Regulation for data privacy in the EU.
Platforms that comply with these regulations ensure that digital signatures are legally valid and enforceable across jurisdictions. This is particularly important for multinational corporations that conduct business in diverse regulatory environments. A 2025 Deloitte report emphasized that compliance is a top priority for 87% of organizations adopting digital signature solutions.
Quick Win:
Verify that the digital signature solution you use complies with the most relevant regulations for your industry and region. Consider solutions like Zignature's secure platform features for guaranteed compliance.
5. Role-Based Access Control (RBAC)
Role-Based Access Control (RBAC) is a security feature that allows organizations to define user roles and permissions based on their specific responsibilities. In 2026, this feature is crucial for preventing unauthorized access to sensitive documents and ensuring secure workflows.
For example, in a financial organization, an administrator might grant access to client contracts only to senior managers and restrict viewing permissions for junior staff. An NIST study found that RBAC reduces internal data breaches by 62% by limiting the exposure of sensitive information.
Key Takeaways:
- Implement RBAC to control access to sensitive documents based on user roles.
- Regularly review user permissions to ensure they align with current responsibilities.
6. Advanced Biometric Verification
Biometric verification is rapidly becoming a standard feature in digital signature solutions, providing an unparalleled level of security by using unique biological traits to verify a user's identity. Common biometric methods include:
- Fingerprint recognition.
- Facial recognition.
- Voice authentication.
In healthcare, for instance, biometric verification ensures that only authorized professionals can approve sensitive patient consent forms. A Biometric Update study predicts that by 2026, 75% of digital signature platforms will include biometric verification as a default feature.
However, relying solely on biometrics without a backup authentication method can lead to user frustration. Always pair biometrics with an alternative verification method, such as OTPs, for a seamless user experience.
FAQ
Q1: Are digital signatures legally binding worldwide?
Yes, but the legality depends on compliance with region-specific regulations like eIDAS, ESIGN, and UETA.
Q2: How can I ensure my digital signature solution is secure?
Look for features like AES-256 encryption, MFA, audit trails, and compliance with global standards.
Q3: What industries benefit most from secure digital signature solutions?
Industries like healthcare, finance, real estate, and legal services benefit significantly due to their reliance on sensitive data and regulatory compliance.
Q4: How do tamper-evident seals work?
They use cryptographic hashing to lock document data, making any alteration detectable.
Q5: What is the cost of implementing a secure digital signature solution?
Costs vary, but investing in a secure platform like Zignature's solutions ensures long-term ROI through efficiency and compliance.
To further enhance your digital workflows, explore our sister platforms: Apparatuz for workflow automation, Applicantz for recruitment management, Schedly for scheduling and appointments, Supportly for customer support, and Zatisfied for feedback management. Together, these tools create a comprehensive ecosystem that complements your digital signature strategy.