
Electronic signatures (e-signatures) have transformed the way businesses and individuals handle agreements, contracts, and approvals. By providing a convenient, paperless alternative to traditional signatures, e-signatures have revolutionized workflows across industries. However, with the increasing reliance on digital tools, concerns about security, authenticity, and compliance have grown. Are electronic signatures truly secure? What technologies protect them? How do they adhere to regional and global regulations? This comprehensive guide delves into the technology, security protocols, and legal frameworks that underpin e-signatures, ensuring they are both reliable and safe.
The Evolution of E-Signatures: From Convenience to Security
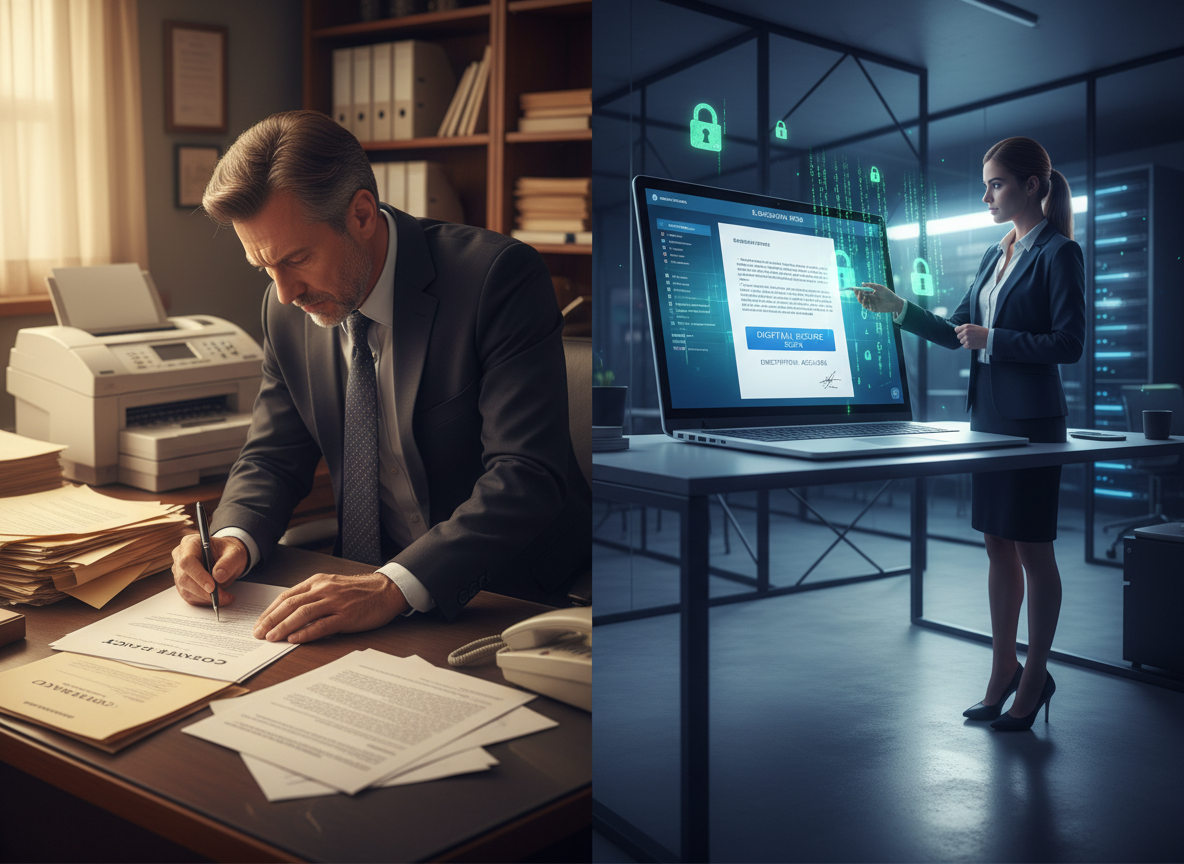
Electronic signatures originated as a simple convenience—a way to sign documents without the inefficiencies of printing, scanning, mailing, or faxing. However, as digital transactions became more prevalent, the focus shifted from ease of use to ensuring that these signatures were secure, authentic, and legally binding. This journey has been marked by key milestones that have shaped the modern e-signature landscape.
In 2000, the United States passed the Electronic Signatures in Global and National Commerce (ESIGN) Act, which granted electronic signatures the same legal standing as traditional handwritten signatures. This was a pivotal moment, as it established the legal and regulatory groundwork for the technology’s adoption. Similarly, in 2016, the European Union implemented the eIDAS (Electronic Identification, Authentication, and Trust Services) regulation, creating a standardized framework for electronic identification and trust services across member states. These regulations not only legitimized e-signatures but also set minimum standards for security and authenticity.
Today, the global e-signature market is thriving. According to a Statista report, the market is projected to grow to $15 billion by 2026, with adoption rates increasing across industries like finance, healthcare, real estate, and legal services. However, this rapid growth has also attracted cybercriminals, making robust security measures more critical than ever.
Why Are E-Signatures Essential in Modern Business?
Beyond convenience, e-signatures have become a cornerstone of operational efficiency. Organizations leveraging e-signature platforms report faster transaction times, reduced dependency on physical resources, and significant cost savings. For instance, a real estate company can finalize property contracts in hours instead of days, while a healthcare provider can secure patient consent for procedures without the need for in-person meetings.
Furthermore, e-signatures play a critical role in global commerce. As businesses expand across borders, the need for secure and universally recognized signing methods has grown. E-signatures allow companies to maintain compliance with international laws while streamlining cross-border agreements. For example, a multinational corporation signing deals with partners in the EU and Asia can rely on e-signature solutions that adhere to both eIDAS and local Asian regulations.
Pro Tip:
When adopting an e-signature solution, assess its integrations with other tools in your tech stack, such as customer relationship management (CRM) systems or document management platforms. Seamless integration ensures a smoother workflow and maximizes efficiency.
Key Takeaway:
- E-signatures have evolved from a tool of convenience to a technology focused on security and compliance.
- Legal frameworks like ESIGN and eIDAS have legitimized e-signatures globally.
- The market’s rapid growth highlights the need for advanced security measures to prevent cyberattacks.
Encryption: The Backbone of E-Signature Security
Encryption is the cornerstone of e-signature security, protecting the confidentiality and integrity of data during transmission and storage. But what exactly is encryption, and how does it safeguard electronic signatures?

At its core, encryption is the process of converting plain text into an unreadable format, which can only be deciphered using a cryptographic key. In the context of e-signatures, encryption ensures that sensitive data, such as the signed document and the user’s credentials, cannot be accessed or altered by unauthorized parties.
How Do Different Encryption Methods Compare?
Most e-signature platforms rely on two primary types of encryption:
- Symmetric Encryption: Uses a single key for both encryption and decryption. While fast and efficient, it requires secure key distribution between parties.
- Asymmetric Encryption: Employs a pair of keys—a public key for encryption and a private key for decryption. This method is more secure, as the private key is never shared.
| Encryption Type | Advantages | Disadvantages |
|---|---|---|
| Symmetric Encryption | Fast and efficient | Requires secure key sharing |
| Asymmetric Encryption | Highly secure; private key remains confidential | Slower due to computational complexity |
The industry standard for encryption is Advanced Encryption Standard (AES) with 256-bit keys, which is considered virtually unbreakable with current technology. AES-256 is widely used by governments, financial institutions, and e-signature platforms to encrypt sensitive data. According to the National Institute of Standards and Technology (NIST), this level of encryption ensures that data remains secure even in the face of advanced cyber threats.
The Role of Hashing Algorithms
In addition to encryption, hashing algorithms like SHA-256 play a crucial role in e-signature security. These algorithms generate a unique digital fingerprint for each document, ensuring that any modification to the document invalidates the signature. This feature provides an additional layer of protection against tampering, as any unauthorized changes will disrupt the hash value, rendering the digital signature invalid.
For example, if a signed contract is intercepted and altered, the hashing algorithm will detect the discrepancy, preventing the fraudulent version from being accepted. This makes hashing indispensable for maintaining the integrity of signed documents.
Common Mistake:
Assuming all e-signature platforms offer the same level of encryption. Users should verify that their chosen platform employs AES-256 encryption and robust hashing algorithms.
Quick Win:
Ask your e-signature provider for a security whitepaper that outlines their encryption standards and protocols. This document can help you assess whether their platform meets your security requirements.
Authentication Protocols: Verifying the Signer
Encryption alone cannot prevent fraud if the identity of the signer is not verified. This is where authentication protocols come into play. These protocols ensure that the person signing a document is who they claim to be, adding another layer of security to the e-signature process.

Types of Authentication Methods
E-signature platforms offer various authentication methods, ranging from basic to advanced:
- Email Verification: The most basic form of authentication, which requires the signer to confirm their identity via email.
- Two-Factor Authentication (2FA): Combines something the user knows (like a password) with something they have (like a one-time password sent to their phone) to verify their identity.
- Biometric Authentication: Utilizes unique biological traits, such as fingerprints, facial recognition, or voice recognition, to confirm the signer’s identity.
- Digital Certificates: Issued by trusted Certificate Authorities (CAs), these certificates provide the highest level of assurance by linking the signer’s identity to a cryptographic key.
According to a Forrester study, organizations that implement multi-factor authentication reduce the risk of unauthorized access by 99%. For example, a healthcare provider using biometric authentication for e-signatures can ensure that patient data remains secure and compliant with HIPAA regulations.
Pro Tip:
Opt for an e-signature platform that allows you to customize authentication methods based on the sensitivity of the document. For high-stakes agreements, consider using digital certificates or biometric authentication for added security.
Key Takeaway:
- Authentication protocols are essential for preventing fraud and ensuring the integrity of e-signatures.
- Multi-factor authentication significantly reduces the risk of unauthorized access.
- Digital certificates provide the highest level of security and trust.
Compliance: Meeting Legal and Regulatory Standards
While encryption and authentication ensure the technical security of e-signatures, compliance with legal and regulatory standards is equally important. Businesses must ensure that their e-signature solutions adhere to relevant laws and industry-specific regulations to avoid legal complications.

Key compliance features to look for in an e-signature platform include:
- Audit Trails: Detailed logs that record every action taken during the signing process, including timestamps, IP addresses, and user activity.
- Data Residency: Ensures that data is stored within specific geographic regions to comply with local laws, such as the General Data Protection Regulation (GDPR) in Europe.
- Customizable Workflows: Allows organizations to tailor the signing process to meet specific regulatory requirements, such as HIPAA for healthcare or FINRA for financial services.
For instance, a financial services firm operating in multiple countries must ensure that its e-signature platform complies with both local and international regulations. By choosing a solution with built-in compliance features, the firm can avoid costly fines and legal disputes.
According to a Gartner report, 67% of organizations face compliance challenges when adopting digital workflows. This statistic underscores the importance of selecting a solution that simplifies regulatory adherence.
Checklist for Compliance:
- Ensure the platform offers detailed audit trails.
- Verify that data residency options align with your legal obligations.
- Check for industry-specific certifications, such as HIPAA or SOC 2 compliance.
Quick Win:
Conduct a compliance audit of your current e-signature platform to ensure it meets all relevant legal and regulatory requirements. Look for features like audit trails, data residency options, and customizable workflows.
FAQ: Addressing Common Concerns
Are electronic signatures legally binding?
Yes, electronic signatures are legally binding in most jurisdictions, provided they comply with regulations like the ESIGN Act in the U.S. or eIDAS in the EU.
How secure is my data during the signing process?
Most reputable e-signature platforms use AES-256 encryption, secure cloud storage, and advanced authentication protocols to protect your data.
Can electronic signatures be forged?
While no system is entirely immune, features like digital certificates, hashing algorithms, and multi-factor authentication make forgery extremely difficult.
What happens if someone alters a signed document?
Any alteration to a signed document invalidates the digital signature, as the unique hash generated during signing will no longer match.
Conclusion
Electronic signatures offer a powerful combination of convenience, efficiency, and security. By leveraging advanced encryption technologies, robust authentication protocols, and comprehensive compliance measures, e-signature platforms provide businesses with a reliable and legally binding way to conduct digital transactions. As the market continues to grow, organizations must prioritize security and compliance to fully realize the benefits of this transformative technology.
Ready to explore a secure, compliant e-signature solution? Discover Zignature's advanced features and learn how we ensure the highest levels of trust and security.
To further enhance your digital workflows, explore our sister platforms: Apparatuz for workflow automation, Applicantz for recruitment management, Schedly for scheduling and appointments, Supportly for customer support, and Zatisfied for feedback management. Together, these tools create a comprehensive ecosystem that complements your digital signature strategy.