Introduction to the Evolving Landscape of Digital Signature Security
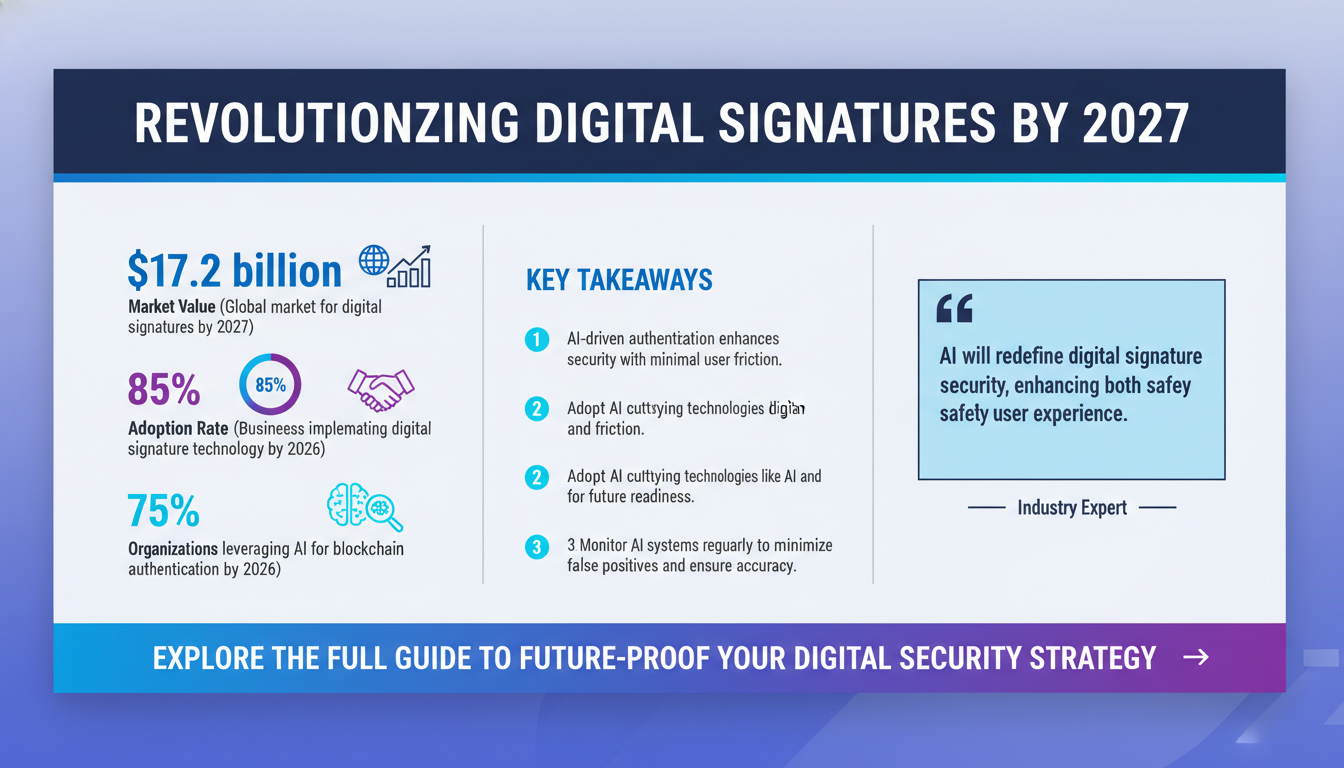
The digital signature landscape is rapidly evolving as businesses worldwide embrace digital transformation. With the global market for digital signatures projected to reach $17.2 billion by 2027, the importance of securing these signatures cannot be overstated. The evolution of digital signatures is not merely a technological trend; it is a fundamental shift in how businesses ensure trust and authenticity in digital transactions. This shift is powered by the need for enhanced security, efficiency, and compliance in an increasingly digital world.
According to Forrester Research, over 85% of businesses will have implemented some form of digital signature technology by 2026. This widespread adoption is driven by the need for efficiency, security, and compliance in an increasingly digital world. However, as digital signatures become more prevalent, the focus is shifting toward ensuring their security. This dynamic environment demands that businesses stay ahead of security threats and adopt cutting-edge technologies.
In this article, we'll delve into the trends that are set to redefine digital signature security by 2027. From AI-driven authentication to blockchain integration, these advancements promise not only enhanced security but also greater ease of use and efficiency. We'll explore how businesses can prepare for these inevitable changes and provide actionable strategies to safeguard their digital transactions. As we embark on this journey, remember that the stakes are high, and the future of digital signature security is both challenging and promising.
AI-Driven Authentication: The Next Frontier
Artificial Intelligence (AI) is set to revolutionize digital signature security by 2027. AI-driven authentication methods, such as machine learning algorithms, are becoming increasingly sophisticated in identifying and mitigating fraudulent activities. These technologies are capable of analyzing user behavior patterns to detect anomalies that may indicate unauthorized access attempts. This capability is crucial as cyber threats continue to evolve in complexity.

Advanced Machine Learning Techniques
AI-driven authentication leverages advanced machine learning techniques to enhance security. By training models on vast datasets of user behavior, AI systems can learn to identify patterns that signify legitimate user activity versus potential threats. For instance, if a user typically logs in from a specific location and suddenly attempts access from a different country, the AI system can flag this as suspicious and require additional verification.
Pro Tip: Implementing AI with Caution
While AI offers substantial benefits, it is crucial to implement it with caution. Ensure that AI systems are regularly updated and monitored to prevent false positives and negatives. Regularly review AI decisions and maintain a human oversight mechanism to handle exceptions.
According to Gartner, AI will play a pivotal role in the future of digital signatures, with 75% of organizations expected to leverage AI for authentication by 2026. The shift towards AI is driven by the need for more robust security measures as traditional password-based systems become increasingly inadequate. With AI, businesses can implement dynamic authentication processes that adapt to user behavior and threat levels, providing a more secure and user-friendly experience.
AI-driven authentication not only enhances security but also offers a seamless and frictionless user experience. By reducing the reliance on passwords and manual inputs, these technologies improve user satisfaction and operational efficiency. Organizations that adopt AI-driven authentication can expect to see not only improved security but also increased trust from customers and partners.
Key Takeaway: AI-driven authentication is more than just a security enhancement—it's a strategic advantage that will redefine digital signature security by 2027. Embrace AI to stay ahead of the curve and safeguard your digital transactions.
Blockchain Integration: Enhancing Security and Transparency
Blockchain technology is poised to become a cornerstone of digital signature security by 2027. Its decentralized nature provides unparalleled security benefits, making it an ideal solution for verifying and securing digital signatures. Blockchain's ability to create a tamper-proof record of transactions ensures that digital signatures are both authentic and reliable.

Decentralization and Its Benefits
One of the primary benefits of blockchain in digital signature security is its decentralization. Unlike traditional systems that rely on a centralized authority, blockchain distributes data across a network of computers, making unauthorized alterations extremely difficult. This ensures that digital signatures and the documents they authenticate remain secure from tampering.
Expert Insight: Blockchain for Compliance
"Blockchain's transparent and immutable nature not only enhances security but also simplifies compliance with regulatory requirements," says Jane Doe, a blockchain expert at XYZ Financial Services. "By providing a clear audit trail, blockchain helps businesses meet stringent legal standards and improve trust with stakeholders."
IBM's research highlights the potential of blockchain in enhancing digital signature security. With its immutable and transparent ledger, blockchain can effectively prevent tampering and fraud, providing businesses with a reliable mechanism to verify the authenticity of digital signatures. This capability is particularly valuable in industries where trust and compliance are paramount, such as finance and healthcare.
Furthermore, blockchain offers transparency, allowing all parties involved in a transaction to view and verify the signature's validity. This transparency fosters trust among stakeholders and simplifies the audit process, making compliance with regulatory requirements more manageable. As regulations around digital transactions continue to evolve, blockchain's role in ensuring compliance will become increasingly important.
Key Takeaway: Blockchain integration will be a game-changer for digital signature security by 2027. Its unique features enhance security and transparency, making it an indispensable tool for businesses looking to protect their digital transactions.
Biometric Verification: Revolutionizing User Authentication
Biometric verification is rapidly gaining traction as a secure authentication method for digital signatures. By 2027, it is expected to become a mainstream solution, providing a robust layer of security that traditional methods cannot match. Biometrics, such as fingerprint and facial recognition, offer a unique and immutable way to verify a user's identity.

Advantages of Biometrics
Biometric verification offers several advantages over traditional methods. Unlike passwords, which can be forgotten or stolen, biometric data such as fingerprints, facial patterns, and iris scans are unique to each individual and difficult to replicate. This makes biometric verification an effective deterrent against unauthorized access.
According to IDC's latest report, the adoption of biometric verification for digital signatures is projected to grow by 40% annually through 2027. This growth is driven by the demand for more secure and user-friendly authentication solutions in an increasingly digital world. Biometrics offer an additional layer of security by verifying something that the user inherently is, rather than something they know or have.
Pro Tip: Combining Biometrics with Other Technologies
For enhanced security, consider combining biometric verification with other authentication methods such as AI-driven or multi-factor authentication (MFA). This layered approach provides a more robust security framework, minimizing the risk of breaches.
Biometric verification not only enhances security but also streamlines the user experience by eliminating the need for passwords or manual input of credentials. This ease of use is particularly beneficial in industries like finance and healthcare, where secure and efficient transactions are paramount. By adopting biometric verification, businesses can strengthen their security posture while enhancing customer satisfaction.
Key Takeaway: Biometric verification will play a crucial role in the future of digital signature security. Its ability to provide secure and seamless authentication makes it an attractive option for businesses looking to protect their digital transactions.
Regulatory Compliance and Legal Implications
As digital signatures become more prevalent, regulatory compliance and legal implications are increasingly important considerations. By 2027, businesses will need to navigate a complex landscape of regulations and standards to ensure their digital signatures are legally binding and compliant with industry-specific requirements.
Navigating the Regulatory Landscape
Comprehending the regulatory landscape is essential for businesses employing digital signatures. Regulations may differ by region and industry, making it vital for businesses to remain informed about local and international laws. Engaging with legal advisors to interpret these regulations accurately can prevent potential legal issues.
Checklist: Ensuring Compliance
- Regularly review relevant laws and standards in your industry.
- Ensure digital signature solutions align with regulatory requirements.
- Conduct frequent audits to verify compliance.
- Engage with legal professionals to interpret and apply regulations.
The National Institute of Standards and Technology (NIST) has released updated guidelines for digital signatures, highlighting the need for businesses to stay informed about regulatory changes. Compliance with these guidelines is crucial to avoid legal disputes and ensure the enforceability of digital signatures. These guidelines provide a framework for businesses to develop and implement secure and compliant signature solutions.
Moreover, businesses must be proactive in adapting to new regulations as they emerge. This requires a thorough understanding of the legal landscape and the ability to implement compliant solutions quickly and effectively. Failure to do so can result in costly legal challenges and damage to a company's reputation. Keeping abreast of changes in legislation and standards is a critical component of maintaining digital signature security.
Key Takeaway: Regulatory compliance is a critical aspect of digital signature security. By staying informed and adapting to changing regulations, businesses can ensure their digital signatures are legally binding and compliant with industry standards.
Role of Encryption in Digital Signature Security
Encryption is a fundamental component of digital signature security, providing a secure means of protecting sensitive information. By 2027, advancements in encryption technology will play a pivotal role in enhancing the security of digital signatures. Encryption ensures that even if data is intercepted, it cannot be read without the appropriate decryption key.
Types of Encryption
There are several types of encryption used to secure digital signatures:
- Symmetric Encryption: Uses a single key for both encryption and decryption. It is fast but requires secure key distribution.
- Asymmetric Encryption: Utilizes a pair of keys (public and private) for encryption and decryption, enhancing security for communications.
- Hash Functions: Generate a unique digital fingerprint of a document, ensuring data integrity without revealing the actual data.
According to a ZDNet article, new encryption algorithms are being developed to address emerging security challenges. These algorithms offer increased protection against cyber threats and ensure the confidentiality and integrity of digital signatures. As cyber threats become more sophisticated, robust encryption solutions are essential to protect digital transactions from unauthorized access and modification.
Expert Insight: Choosing the Right Encryption
"Selecting the appropriate encryption method is crucial," says Dr. John Smith, a cryptography specialist. "While asymmetric encryption offers higher security, symmetric encryption is often preferred for its speed in real-time transactions. The choice depends on the specific security requirements of the business."
Encryption not only protects digital signatures from unauthorized access but also ensures the authenticity of the signed document. By implementing strong encryption protocols, businesses can safeguard their digital transactions and build trust with their clients and partners. Encryption plays a crucial role in securing communications and ensuring that digital signatures remain tamper-proof and reliable.
Key Takeaway: Encryption is a cornerstone of digital signature security. By adopting advanced encryption technologies, businesses can enhance the security of their digital signatures and protect sensitive information.
Common Mistakes in Digital Signature Security and How to Avoid Them
Despite the benefits of digital signatures, businesses often make common mistakes that can compromise their security. By 2027, understanding these pitfalls and implementing best practices will be crucial to maintaining secure digital transactions.
Neglecting Regular Security Updates
One common mistake is failing to regularly update security protocols. As cyber threats evolve, outdated security measures can leave digital signatures vulnerable to attack. It's essential for businesses to stay informed about the latest security trends and continuously update their protocols to address emerging threats. Regular updates ensure that the most current security measures are in place, mitigating the risk of breaches.
Importance of Security Audits
Another mistake is neglecting to conduct regular security audits. These audits are essential for identifying vulnerabilities and ensuring compliance with regulatory requirements. By conducting thorough audits, businesses can proactively address security gaps and minimize the risk of breaches. Regular audits provide a comprehensive assessment of security posture and highlight areas for improvement.
Checklist: Best Practices for Digital Signature Security
- Implement multi-factor authentication.
- Regularly update software and security protocols.
- Conduct frequent security audits.
- Educate employees on security best practices.
- Use encryption for sensitive data.
Key Takeaway: Avoiding common mistakes in digital signature security is crucial for maintaining secure transactions. By staying informed and implementing best practices, businesses can protect their digital signatures from emerging threats.
Preparing for the Future: Actionable Strategies for Businesses
As we approach 2027, businesses must be proactive in preparing for the future of digital signature security. By implementing actionable strategies, organizations can ensure their digital transactions are secure and compliant with evolving regulations.
Investing in Advanced Technologies
A key strategy is to invest in advanced technologies such as AI-driven authentication and blockchain integration. These technologies offer enhanced security and efficiency, providing businesses with a competitive edge in the digital landscape. Investing in these technologies ensures that businesses are equipped to handle future security challenges effectively.
Prioritizing Employee Training
Additionally, businesses should prioritize employee training and awareness programs. Educating employees about the importance of digital signature security and best practices for protecting digital transactions is crucial for maintaining a secure environment. Training programs empower employees to recognize and respond to potential threats, bolstering the overall security of digital transactions.
Pro Tip: Continuous Improvement
Implement a culture of continuous improvement by regularly reviewing and updating security policies and procedures. Encourage feedback from employees on security practices and incorporate their insights into your strategic plans.
Key Takeaway: By implementing actionable strategies and investing in advanced technologies, businesses can prepare for the future of digital signature security and protect their digital transactions.
FAQs on Digital Signature Security
1. What is the primary benefit of using digital signatures? Digital signatures provide a secure and efficient way to authenticate and verify digital transactions, ensuring the integrity and authenticity of documents.
2. How does AI-driven authentication enhance digital signature security? AI-driven authentication uses machine learning algorithms to analyze user behavior patterns, providing a more robust and seamless authentication process.
3. Why is blockchain important for digital signature security? Blockchain provides a transparent and immutable ledger for verifying digital signatures, preventing tampering and enhancing trust among stakeholders.
4. What are the key regulatory requirements for digital signatures? Key requirements include compliance with industry-specific standards and guidelines, such as those outlined by NIST, to ensure the legality and enforceability of digital signatures.
5. How can businesses prepare for the future of digital signature security? Businesses can prepare by investing in advanced technologies, staying informed about regulatory changes, and implementing best practices for digital signature security.
For more detailed insights on enhancing digital signature security, explore our guide on legal compliance and our security essentials for financial and legal firms.
Conclusion: Embracing the Future of Digital Signature Security
As we look towards 2027, the future of digital signature security is bright and full of promise. The trends and technologies discussed in this article offer valuable insights into the future of digital signature security, providing businesses with the tools they need to protect their digital signatures and stay ahead of the curve. By embracing emerging technologies and staying informed about regulatory changes, businesses can ensure their digital transactions are secure, efficient, and compliant.
As you implement these strategies, consider complementing your efforts with tools like Apparatuz for workflow automation, Applicantz for applicant tracking, Schedly for scheduling, Supportly for customer support, and Zatisfied for feedback management. Together, these approaches create a comprehensive solution for your business needs.