
In the ever-evolving world of business, where transactions often involve significant sums and sensitive information, ensuring security and preventing fraud have become critical priorities. Whether it’s a multinational corporation conducting cross-border trade or a healthcare provider managing confidential patient data, the need for secure, foolproof methods to protect documents and verify identities cannot be overstated. In this high-stakes environment, digital signatures have emerged as a transformative tool, offering unmatched security, authenticity, and validity for business transactions.
Digital signatures leverage advanced cryptographic technologies to ensure the integrity and authenticity of electronic documents. Unlike traditional pen-and-paper signatures, which are susceptible to forgery and tampering, digital signatures provide a robust framework for verifying identities, ensuring document integrity, and meeting strict compliance requirements. This article explores five key ways digital signatures prevent fraud and enhance security in the most critical business scenarios. By the end, you’ll have a clear understanding of how implementing digital signatures can safeguard your organization against fraud and legal vulnerabilities.
1. Authenticating Signatory Identity to Prevent Impersonation
One of the most prevalent risks in business transactions, especially those conducted digitally, is the possibility of identity fraud. Fraudsters often impersonate authorized personnel to gain access to sensitive information or execute unauthorized transactions. Digital signatures provide a robust solution to this challenge by leveraging advanced cryptographic methods to securely authenticate the identity of signatories.

Digital signatures rely on Public Key Infrastructure (PKI) technology, which uses a pair of cryptographic keys: a private key, held exclusively by the signer, and a corresponding public key that anyone can use to verify the signature. When a document is signed digitally, the signer’s private key encrypts the data, creating a unique digital signature. This signature can only be validated using the corresponding public key, ensuring that the signer’s identity is authenticated.
However, PKI is only one part of the equation. Leading digital signature platforms, such as DocuSign and Zignature, incorporate additional layers of security through multi-factor authentication (MFA). MFA requires signatories to verify their identity using multiple methods, such as biometrics (fingerprints or facial recognition), one-time passwords (OTPs) sent to a registered device, or even geolocation-based verification. This multi-pronged approach significantly reduces the likelihood of unauthorized access, making it nearly impossible for fraudsters to impersonate legitimate signatories.
For example, in 2025, a major global financial institution thwarted a $10 million fraud attempt when its digital signature system detected a discrepancy between a signatory’s biometric data and the stored authentication records. Such instances highlight the critical role that digital signatures play in preventing identity fraud.
According to a Gartner report, organizations that adopt digital signatures experience a 70% reduction in identity fraud incidents. This statistic underscores the effectiveness of digital signatures in high-stakes scenarios where the stakes are simply too high for missteps.
The Role of Biometrics in Identity Verification
Biometric authentication has gained significant traction as part of digital signature systems. Fingerprints, facial recognition, and even voice authentication provide an additional layer of security by relying on unique biological traits that are difficult to replicate. For instance, healthcare institutions frequently use biometric-based digital signatures to ensure that only authorized personnel can access patient records, thereby reducing the risk of data breaches.
Additionally, advancements in artificial intelligence (AI) have further improved the accuracy of biometric systems. AI-driven systems can now detect spoofing attempts, such as the use of photos or masks, making biometric authentication even more foolproof.
Pro Tip: Regularly Update Authentication Methods
Cybercriminals are constantly evolving their tactics. To stay ahead, organizations should periodically update their authentication methods and implement adaptive authentication technologies. These systems analyze user behavior, such as typing speed or login patterns, to identify anomalies that may indicate fraudulent activity.
2. Eliminating Document Tampering with Cryptographic Hashing
Document tampering is a significant issue in business, particularly in industries where contracts, agreements, and sensitive data are exchanged. Alterations to documents can lead to legal disputes, financial losses, and reputational damage. Digital signatures address this problem with cryptographic hashing, a technology that ensures the integrity of signed documents.
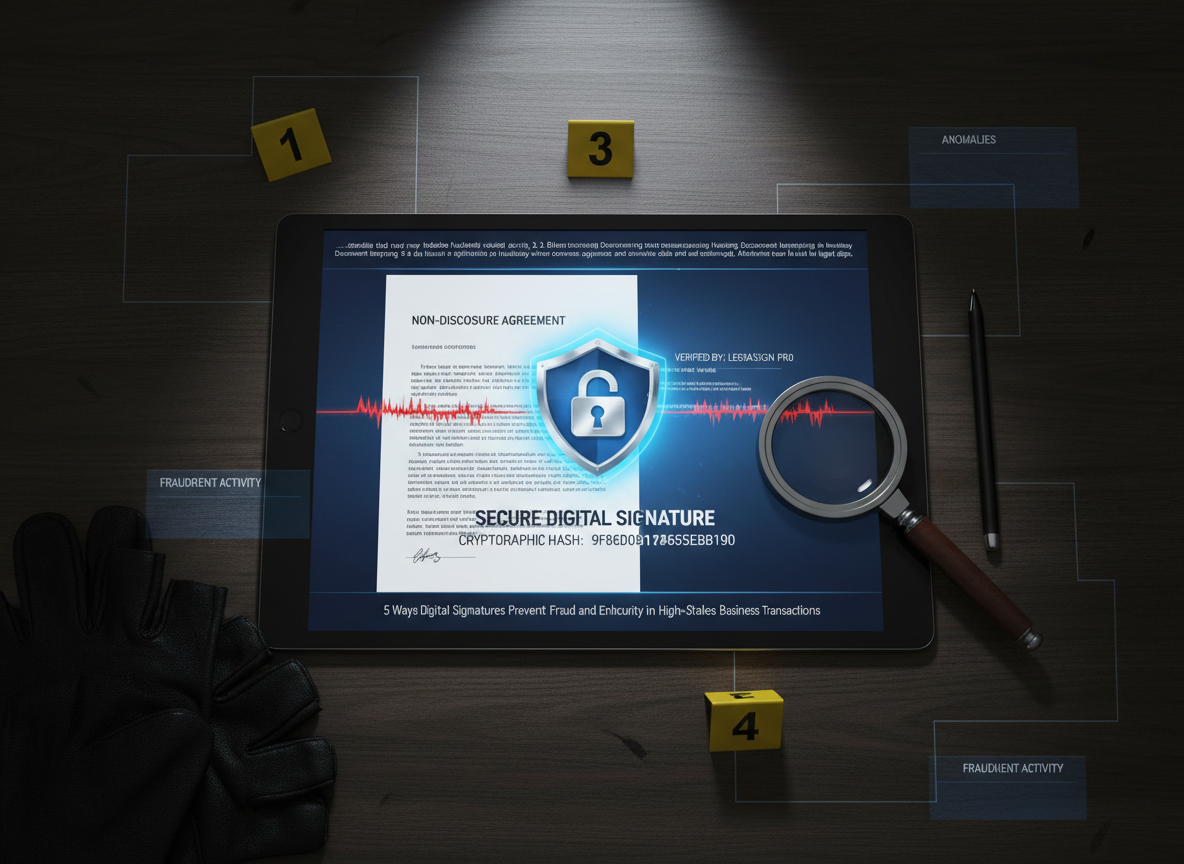
When a document is signed digitally, the system generates a unique cryptographic hash value based on its content. This hash serves as a digital fingerprint for the document. If even a single character within the document is modified after signing, the hash value will change, rendering the digital signature invalid. This provides a clear indication of tampering, ensuring that any unauthorized alterations are immediately detected.
Moreover, some advanced digital signature solutions offer automated tamper alerts. For example, if a signed document is altered in any way, the system can notify all parties involved and provide a detailed audit trail of the changes. This not only prevents fraud but also simplifies the investigative process in case of a breach.
Research from Forrester highlights that businesses utilizing cryptographic hashing as part of their digital signature process reduce document tampering incidents by as much as 85%. This makes it an essential feature for any organization engaging in high-value transactions.
In a well-documented case, a real estate firm avoided a costly litigation process when its digital signature platform flagged a tampered contract. By comparing the original hash value with the altered document’s hash, the company was able to prove the unauthorized changes and avoid financial losses.
How Cryptographic Hashing Works
The cryptographic hashing process involves converting document data into a fixed-length string of characters, regardless of the document’s original size. This hash value is unique to the document’s content, much like a fingerprint. Common hashing algorithms include SHA-256 and SHA-3, which are known for their robustness and resistance to collisions (two different inputs generating the same hash).
Organizations often integrate cryptographic hashing into their document workflows to ensure that every signed document is tamper-proof. For instance, financial institutions use hashing to secure loan agreements, ensuring that terms cannot be altered post-signing without detection.
Expert Insight: Using Blockchain for Enhanced Tamper Detection
Some businesses are now leveraging blockchain technology in conjunction with digital signatures. Blockchain’s decentralized ledger records every signed document’s hash, creating an immutable record that further enhances tamper detection. This approach is particularly useful for industries like supply chain management, where transparency and traceability are critical.
3. Improving Compliance with Regulatory Standards
In industries such as healthcare, finance, and legal services, compliance with regulatory standards is non-negotiable. Failure to adhere to these regulations can result in severe penalties, legal challenges, and reputational harm. Digital signatures help organizations meet compliance requirements by offering features like automated audit trails, secure storage, and adherence to industry-specific standards.

For instance, the eIDAS Regulation in Europe provides a legal framework for electronic transactions within the European Union. Similarly, the ESIGN Act in the United States ensures the legal validity of electronic signatures in interstate and foreign commerce. Digital signature platforms are designed to comply with these regulations, providing businesses with the tools they need to stay compliant.
Healthcare organizations, for example, often rely on digital signatures to comply with the Health Insurance Portability and Accountability Act (HIPAA). By utilizing digital signatures, healthcare providers can ensure that patient information is securely stored and accessed only by authorized individuals. Additionally, digital signatures can be configured to comply with the General Data Protection Regulation (GDPR) for data privacy, as well as ISO/IEC 27001 standards for information security.
A pharmaceutical company in Europe serves as a real-world example. After implementing an eIDAS-compliant digital signature solution, the company reduced its regulatory violations by 90%. The solution’s automated audit trails and compliance monitoring features allowed the company to identify and address potential issues before they became problems.
Industry-Specific Compliance Examples
In the financial sector, compliance with regulations like the Sarbanes-Oxley Act (SOX) and the Payment Card Industry Data Security Standard (PCI DSS) is critical. Digital signatures provide the necessary tools to meet these requirements, including traceable audit trails and secure storage solutions. Similarly, in the legal profession, digital signatures ensure compliance with jurisdiction-specific electronic signature laws, enabling lawyers to manage contracts and agreements securely.
In the education sector, digital signatures are increasingly used to authenticate diplomas and transcripts, ensuring compliance with accreditation standards and preventing credential fraud.
Pro Tip: Regular Compliance Audits
Conduct regular compliance audits to ensure that your digital signature processes align with evolving regulatory requirements. Work closely with compliance officers and legal teams to address any gaps in your workflows.
4. Enhancing Security with Advanced Encryption
Encryption is the cornerstone of digital signature security. By encoding information in a way that only authorized parties can access, encryption ensures that sensitive data remains secure during high-stakes transactions. Modern digital signature platforms leverage advanced encryption algorithms such as RSA and elliptic curve cryptography (ECC) to provide robust security.
RSA encryption, for example, uses large key sizes to secure data, making it computationally infeasible for hackers to break. ECC, on the other hand, achieves the same level of security with smaller key sizes, making it faster and more efficient. Both methods are highly effective in protecting digital signatures and the documents they are attached to.
An IDC study found that organizations using encrypted digital signature platforms experience 60% fewer data breaches compared to those relying on traditional methods. This statistic highlights the importance of encryption in protecting sensitive business information.
Choosing the Right Encryption Algorithm
When selecting a digital signature platform, consider the encryption algorithm it uses. For high-security applications, platforms offering 256-bit encryption or higher are recommended. These algorithms provide a virtually unbreakable layer of security for sensitive documents.
Expert Insight: The Role of Quantum Computing
While current encryption methods are robust, the advent of quantum computing poses potential risks. Forward-thinking organizations are exploring quantum-resistant encryption algorithms to future-proof their digital signature systems against emerging threats.
5. Mitigating Legal Risks with Non-Repudiation
Non-repudiation is a critical feature of digital signatures, ensuring that signatories cannot deny their involvement in a transaction. This is particularly important in legal disputes, where the authenticity of a document may be called into question. Digital signatures address this challenge by creating immutable records that link a signer’s identity to the signed document.
Platforms offering non-repudiation often include features like timestamps, IP tracking, and device authentication. These elements create a comprehensive chain of evidence that can be presented in court, providing irrefutable proof of signer involvement. For example, a Nucleus Research study revealed that businesses using digital signatures reduce litigation costs by 40%, thanks to their ability to provide clear evidence during disputes.
Case Study: Success in Court
In a notable case, a logistics company successfully defended itself in court by presenting a digitally signed contract with detailed metadata, including timestamps and IP addresses. This evidence proved that the claimant had authorized the agreement, saving the company millions in legal fees.
Pro Tip: Leverage Metadata for Legal Security
Ensure your digital signature platform captures comprehensive metadata, including timestamps, geolocation, and device information. This data can be invaluable in resolving disputes quickly and efficiently.
Conclusion
Digital signatures are not just a convenience; they are a necessity in today’s high-stakes business environment. By authenticating identities, preventing document tampering, ensuring compliance, enhancing encryption, and providing non-repudiation, digital signatures offer unparalleled security and fraud prevention capabilities. Organizations that implement these technologies not only protect themselves from fraud but also position themselves as trustworthy, compliant, and forward-thinking entities in their industries.
To get started, explore platforms like Zignature, which offers advanced features tailored for secure, high-stakes transactions. Take the first step toward safeguarding your business by adopting digital signatures today.
To further enhance your digital workflows, explore our sister platforms: Apparatuz for workflow automation, Applicantz for recruitment management, Schedly for scheduling and appointments, Supportly for customer support, and Zatisfied for feedback management. Together, these tools create a comprehensive ecosystem that complements your digital signature strategy.