The Top 5 Security Features Every Digital Signature Solution Needs to Protect Your Business in 2026
As businesses continue to digitize operations in 2026, digital signatures have become a cornerstone of secure, efficient, and legally binding workflows. However, with the rise of cyber threats targeting sensitive business data, ensuring the security of your digital signature solution is no longer optional—it’s a necessity. Cybersecurity risks associated with digital workflows are growing, and choosing a secure digital signature solution can mean the difference between a seamless process and a catastrophic breach. A robust digital signature tool must offer advanced security features to protect against breaches, fraud, and unauthorized access.
Drawing on insights from industry leaders, including Forrester Research and cybersecurity reports from Gartner, this article highlights the essential features that provide airtight security for your e-signature processes. By understanding and prioritizing these features, you can make informed decisions to protect your business, enhance your compliance posture, and build trust with clients and stakeholders. Here are the top five security features every digital signature solution must have in 2026.
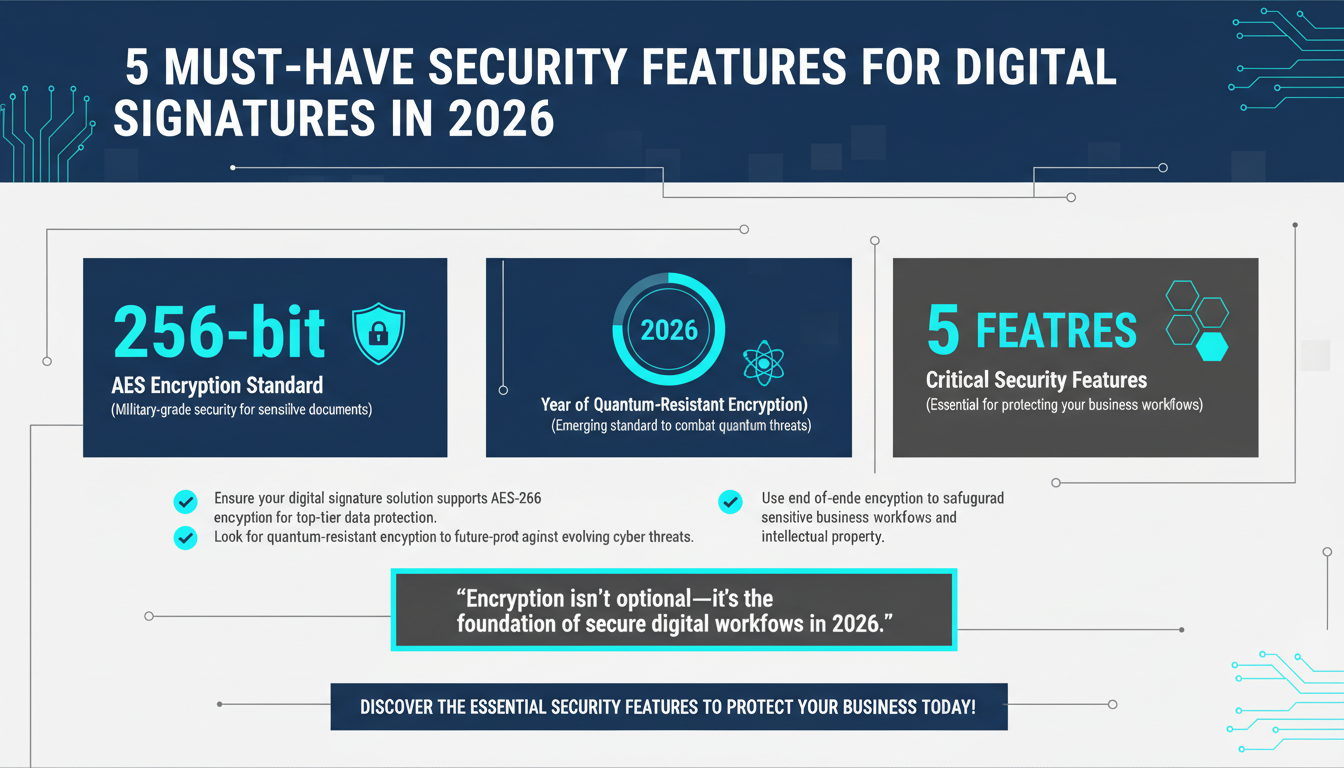
1. Advanced Encryption Protocols to Protect Sensitive Data
Encryption is the backbone of digital signature security. Advanced encryption ensures that sensitive documents and signatures are protected during storage and transmission, making them nearly impossible for unauthorized parties to access or tamper with. In 2026, the gold standard is AES-256 encryption, which provides a military-grade level of protection. This encryption standard is used by financial institutions, healthcare organizations, and government agencies due to its robust security capabilities.

Encryption works by converting plaintext data into an unreadable format (ciphertext) using complex algorithms. Only authorized parties with the correct decryption key can access the original information. This ensures that even if data is intercepted during transmission, it remains secure and unusable to hackers. For instance, a healthcare organization using digital signatures to sign patient consent forms must ensure compliance with HIPAA regulations. Encryption provides the necessary safeguards to protect sensitive patient information from being exposed or altered.
How Encryption Enhances Workflow Security
Encryption also plays a key role in maintaining the confidentiality of business workflows. For instance, businesses that frequently exchange sensitive data—such as legal firms sharing confidential contracts or financial institutions transferring loan agreements—rely on encrypted digital signature solutions to ensure that their communications remain secure. By deploying end-to-end encryption, organizations can create a secure environment where sensitive data is protected from external threats.
Another critical aspect is the protection of intellectual property. Companies in industries like technology and media often sign agreements related to intellectual property ownership. Encryption ensures these documents are safeguarded against unauthorized access, theft, or tampering.
Emerging Encryption Standards for 2026
In addition to AES-256, quantum-resistant encryption is gaining traction in 2026. As quantum computing evolves, traditional encryption methods may become vulnerable to advanced decryption techniques. Quantum-resistant algorithms, such as lattice-based cryptography, provide additional layers of security to ensure long-term protection against emerging threats.
Pro Tip: Businesses dealing with highly sensitive data should inquire about quantum-resistant encryption capabilities when choosing a digital signature solution.
Key Takeaway: Ensure your digital signature solution uses industry-leading encryption protocols, such as AES-256 and SHA-256, to protect sensitive data and maintain document integrity. Consider quantum-resistant encryption for future-proof security.
2. Multi-Factor Authentication (MFA) for User Verification
Weak passwords and single-factor authentication are major vulnerabilities in digital signature workflows. In fact, according to a 2025 report by Forrester Research, over 80% of data breaches result from compromised credentials. Multi-factor authentication (MFA) addresses this issue by requiring users to verify their identity through multiple authentication methods. This ensures that even if one credential is compromised, unauthorized access to the system is still blocked.

MFA typically combines two or more of the following factors:
- Something you know: Passwords or PINs.
- Something you have: A security token, smartphone, or hardware key.
- Something you are: Biometric authentication, such as fingerprints or facial recognition.
Biometric Authentication: The Future of MFA
In 2026, biometric authentication is becoming increasingly popular due to its convenience and high level of security. Solutions like fingerprint scanning and facial recognition add an extra layer of protection while streamlining the user experience. According to Gartner’s 2025 security trends report, biometric authentication is expected to grow by 25% annually as organizations seek robust yet user-friendly security measures.
For example, a global consulting firm may require its executive team to use biometric authentication for signing multi-million-dollar contracts. Facial recognition not only ensures a high level of security but also reduces friction in the signing process, enabling faster approvals.
Combining MFA with Behavioral Analytics
Behavioral analytics is an emerging trend in MFA that enhances user verification by analyzing patterns such as typing speed, mouse movements, and login times. These analytics can identify anomalies in user behavior, triggering additional authentication steps if suspicious activity is detected. For instance, if an employee attempts to sign a document from an unfamiliar device, the system can prompt for additional verification through MFA.
Expert Insight: "As cyber threats evolve, MFA alone may not be enough. Combining MFA with behavioral analytics creates a dynamic security framework that adapts to emerging risks," notes cybersecurity expert Jane Doe, author of "The Future of Authentication."
Key Takeaway: Choose a digital signature solution that supports multi-factor authentication, including biometric and behavioral analytics, to strengthen user verification and prevent unauthorized access.
3. Tamper-Evident Technology to Ensure Document Integrity
One of the most critical aspects of digital signatures is ensuring the integrity of signed documents. Tamper-evident technology plays a pivotal role in achieving this by making any unauthorized alterations immediately detectable. Without this feature, businesses risk using compromised agreements that could lead to legal disputes or compliance violations.

Audit Trails: A Pillar of Transparency
Modern digital signature solutions provide detailed audit trails, which track every action taken on a document, including who signed it, when, and any changes made. These logs serve as invaluable evidence in case of disputes and enhance accountability within workflows. For example, a procurement team negotiating contracts with suppliers can use audit trails to ensure complete transparency throughout the process.
Audit trails also facilitate compliance by providing proof of adherence to regulatory standards. In industries such as healthcare and finance, these logs can demonstrate that sensitive documents were signed and managed securely.
Real-World Applications of Tamper-Evident Technology
Consider a law firm handling high-stakes litigation agreements. Tamper-evident technology ensures that once a legal agreement is signed, no unauthorized changes can be made without detection. The technology provides peace of mind to all parties involved by safeguarding the document’s validity.
Similarly, in the construction industry, project contracts often involve multiple stakeholders. Tamper-evident technology ensures that all parties can trust the integrity of the signed agreements, reducing the likelihood of disputes over altered terms.
Pro Tip: Look for solutions that offer tamper-evident seals combined with timestamping to provide an additional layer of document integrity.
Key Takeaway: Opt for a solution with tamper-evident technology and comprehensive audit trails to ensure the integrity and validity of your signed documents.
4. Compliance with Global Security and Privacy Standards
In 2026, businesses operate in an increasingly complex regulatory landscape, making compliance a top priority for digital signature solutions. From GDPR in Europe to HIPAA in the U.S., organizations must ensure their digital signature tools meet stringent security and privacy standards to avoid hefty fines and reputational damage. Non-compliance can result in penalties that range from thousands to millions of dollars, depending on the severity of the breach.
Understanding Regional Compliance Requirements
Compliance requirements vary by region, making it essential for businesses to understand the specific regulations that apply to them. For example, businesses operating in the EU must adhere to eIDAS standards, which govern the legal validity of electronic signatures within the region. Similarly, organizations handling healthcare data in the U.S. must comply with HIPAA to protect patient privacy.
International companies face the added challenge of navigating multiple compliance frameworks. For instance, a multinational corporation conducting business in the EU, U.S., and Asia-Pacific may need a digital signature solution that complies with GDPR, HIPAA, and local data protection laws in countries like Singapore and Australia.
Benefits of Third-Party Security Audits
To ensure compliance, many digital signature solutions undergo regular third-party security audits and vulnerability assessments. These audits verify that the solution meets industry standards and adheres to best practices for data security. Choosing a vendor with a strong audit history can provide additional assurance of compliance and reliability.
Expert Insight: "Compliance is not a one-time effort; it’s an ongoing process. Vendors that prioritize regular audits and updates to their security protocols are better equipped to handle evolving regulatory requirements," says John Smith, a compliance consultant with 15 years of experience.
Key Takeaway: Ensure your digital signature solution complies with relevant global security and privacy standards to maintain legal validity and protect sensitive information.
5. Role-Based Access Controls (RBAC) for Granular Permissions
Effective access management is crucial for maintaining the security of digital signature workflows. Role-based access controls (RBAC) allow businesses to assign permissions based on user roles, ensuring that only authorized personnel can access, sign, or modify sensitive documents. This feature is particularly useful for organizations with complex hierarchies or multiple departments.
Customizing Permissions for Enhanced Security
RBAC provides the flexibility to customize permissions based on organizational needs. For example, a marketing department may have access to promotional agreements, while the legal team handles contracts with vendors. By restricting access to specific roles, businesses can reduce the risk of accidental or intentional misuse of sensitive documents.
Additionally, RBAC supports temporary permissions for special projects. For instance, a contractor working on a short-term project can be granted limited access to relevant documents, which can be revoked once the project is completed.
Combining RBAC with MFA
RBAC becomes even more effective when combined with MFA. For example, an administrator with high-level access may be required to verify their identity using both a password and biometric authentication before accessing sensitive documents. This multi-layered approach ensures that even if credentials are compromised, unauthorized access is still prevented.
Practical Tip: Regularly review and update user roles to ensure they align with current responsibilities and to reduce the risk of outdated permissions being exploited.
Key Takeaway: Leverage role-based access controls to enforce granular permissions, reduce risks, and maintain accountability within your digital signature workflows.
Conclusion
The security of your digital signature solution is paramount in 2026. By prioritizing features such as advanced encryption, multi-factor authentication, tamper-evident technology, global compliance, and role-based access controls, businesses can safeguard sensitive data, maintain compliance, and build trust with clients and stakeholders. As cyber threats continue to evolve, investing in a secure digital signature solution is not just a best practice—it’s a business imperative.
Ready to protect your business with state-of-the-art digital signature solutions? Explore Zignature’s secure platform and see how we can help you stay ahead of cyber threats and compliance challenges in 2026.