In today's digital age, where data breaches and cyber threats are escalating in both frequency and sophistication, safeguarding sensitive information has become a paramount concern for organizations worldwide. IT and cybersecurity professionals are at the forefront of this battle, tasked with implementing robust security measures to protect valuable data. One such powerful tool that has emerged is the electronic signature, offering not just convenience but also enhanced security to digital transactions. This comprehensive guide explores how electronic signatures can bolster data protection strategies, ensuring that your organization remains resilient against the ever-evolving landscape of cyber threats.
The Evolution of Electronic Signatures in Data Security
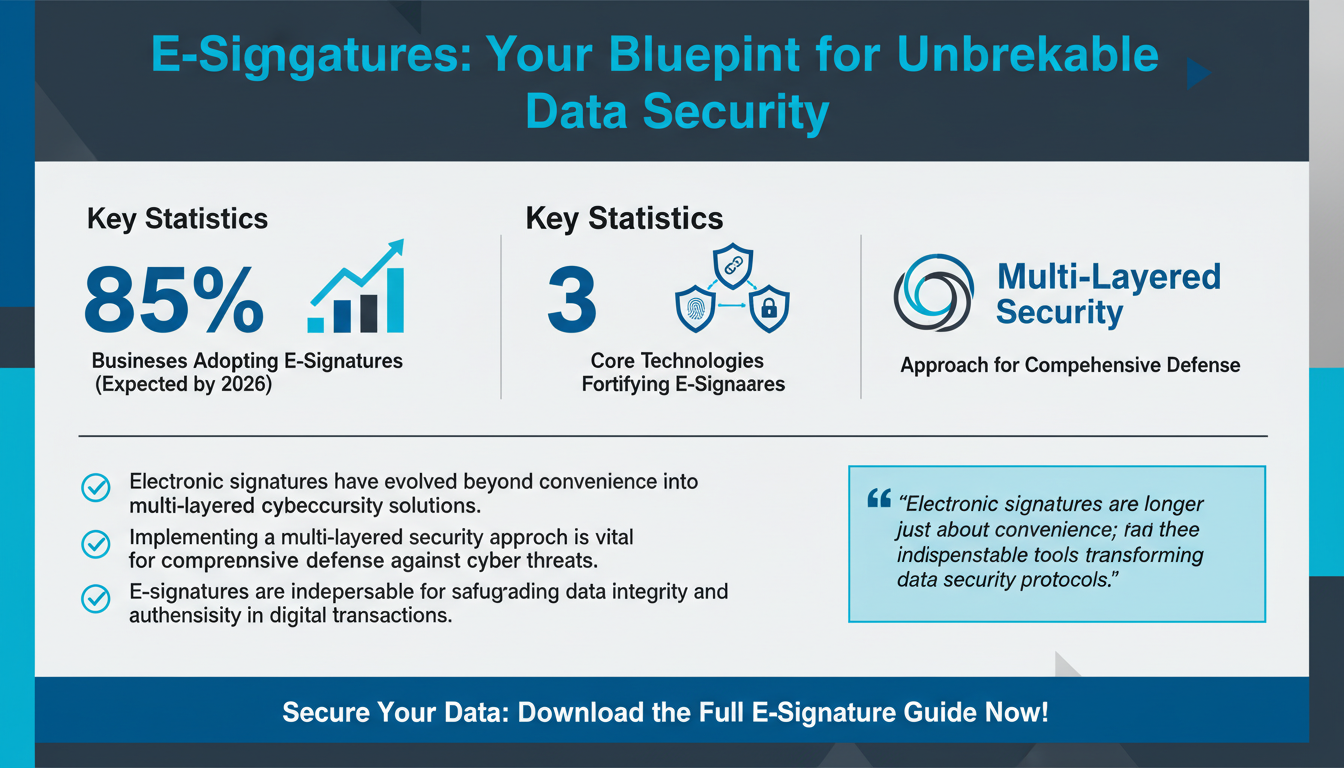
Electronic signatures have undergone significant evolution, transforming from basic digital tools into complex security solutions integral to modern cybersecurity frameworks. Initially, electronic signatures were merely digital versions of handwritten signatures, used for convenience. However, as digital transactions have proliferated, so too has the sophistication of electronic signature technologies. According to Gartner's 2025 Digital Signature Adoption Report, a staggering 85% of businesses are expected to adopt electronic signature solutions by 2026, highlighting their critical role in data security.

The journey of electronic signatures began with simple digital formulations, but today, these signatures integrate multi-layered security features such as encryption, authentication, and comprehensive audit trails. These advancements have transformed electronic signatures into robust tools that facilitate seamless document management while significantly enhancing data security protocols. The integration of biometric verification, blockchain technologies, and advanced encryption algorithms are key developments that have fortified electronic signatures, making them indispensable in the fight against data breaches.
Biometric Verification and Blockchain
Biometric verification, such as fingerprint and facial recognition, adds a personalized layer of security, ensuring that electronic signatures are unique to the individual. This technology not only simplifies the user experience but also significantly reduces the risk of unauthorized access. Companies like Apple and Samsung have incorporated such technologies into their devices, making biometric verification more accessible and reliable.
Blockchain technology, on the other hand, provides a decentralized ledger system that ensures all transactions are transparent and immutable. This technology is particularly effective in preventing fraud, as any attempt to alter a signature or document is immediately visible across the network. For example, the financial sector has been utilizing blockchain for secure transactions, highlighting its effectiveness in maintaining data integrity.
Pro Tip: Leveraging Multi-Layered Security
When integrating electronic signatures into your organization, consider adopting a multi-layered security approach. This involves combining encryption, biometric verification, and blockchain technology to create a comprehensive defense against potential threats. Such an approach not only enhances security but also builds trust with clients and partners.
Understanding the Security Features of Electronic Signatures
Electronic signatures are not merely digital representations of handwritten signatures; they encompass a suite of security features designed to protect the integrity and authenticity of digital documents. A pivotal aspect of these signatures is encryption, which safeguards data by converting it into a secure format that can only be decrypted with a specific digital key.

Authentication mechanisms play a crucial role in verifying the identity of signatories, often employing multi-factor authentication (MFA) to add an extra layer of protection. According to Forrester's research on MFA in digital signatures, companies that implement MFA see a 70% reduction in unauthorized access incidents. This highlights the importance of using robust authentication methods to protect sensitive transactions.
Another vital component is the audit trail, which provides a detailed record of all actions taken on a document. This transparency not only aids in compliance with regulatory standards but also enhances trust between parties by ensuring accountability. The audit trail can track when a document was signed, by whom, and any modifications made, providing an invaluable resource in case of disputes or compliance audits.
Encryption Techniques
Encryption acts as the first line of defense against unauthorized access. Modern electronic signature platforms utilize advanced encryption standards (AES) to protect data. AES-256, for example, is a widely accepted standard for encrypting data, offering a robust level of security against cyber threats.
Expert Insight: Importance of Regular Security Audits
Experts recommend regular security audits to ensure that your electronic signature systems remain secure over time. These audits can help identify potential vulnerabilities and provide insights into improving existing security measures. Engaging third-party cybersecurity firms to conduct these audits can offer an unbiased perspective and leverage their specialized expertise.
Implementing Electronic Signatures: Best Practices for IT Security
While the benefits of electronic signatures are clear, implementing them effectively requires a strategic approach. IT and cybersecurity professionals must ensure that these solutions align with their organization's security policies and regulatory requirements. A well-planned implementation strategy can prevent common pitfalls and maximize the security benefits of electronic signatures.
Conducting a Risk Assessment
The first step in implementation is conducting a comprehensive risk assessment to identify potential vulnerabilities. According to a PwC study on digital signature risk assessment, early identification of risks can reduce security incidents by up to 60%. This involves assessing the organization's current digital infrastructure, identifying weak points in the signature process, and developing strategies to reinforce these areas.
During the risk assessment, it's crucial to evaluate both internal and external threats. Internal threats may involve employee mishandling or inadvertent data exposure, while external threats could include cyberattacks aimed at intercepting sensitive information.
Selecting a Reliable Provider
Next, it is essential to select a reliable electronic signature provider that offers robust security features and complies with relevant regulations, such as the eIDAS Regulation in Europe or the ESIGN Act in the United States. This ensures that the chosen solution not only meets security standards but also supports legal validity. Providers should be evaluated based on their encryption capabilities, authentication methods, and ability to provide detailed audit trails.
Pro Tip: Prioritize Training and Education
Training staff on the correct use of electronic signatures is another critical component. Ensuring that employees understand how to securely sign and manage documents can prevent user-related security breaches and enhance overall data protection. Regular training sessions and updates on new security protocols can keep employees informed and vigilant against potential threats.
Challenges and Solutions in Securing Electronic Signatures
Despite their advantages, electronic signatures are not without challenges. IT and cybersecurity professionals must navigate potential security threats, such as phishing attacks and fraudulent signatures. Addressing these challenges requires a proactive approach and the implementation of advanced security measures.

Mitigating Phishing Attacks
Phishing remains a prevalent threat in the digital landscape, with attackers often targeting electronic signature processes to gain unauthorized access to sensitive information. To combat this, organizations should employ anti-phishing technologies and educate users on recognizing phishing attempts. Dark Reading's insights on anti-phishing technologies offer valuable strategies for enhancing security. Implementing email filters, conducting regular security awareness training, and using secure communication channels are effective measures to mitigate phishing risks.
Ensuring Signature Authenticity
Addressing fraudulent signatures involves implementing verification processes that ensure the authenticity of signatories. Techniques such as digital certificates and blockchain technology can provide tamper-proof verification and traceability, significantly reducing the risk of forgery. Blockchain, with its decentralized and immutable nature, offers a reliable way to verify transactions and ensure that signatures remain unaltered.
Expert Insight: Continuous Monitoring and Updates
Experts stress the importance of continuous monitoring and regular updates to electronic signature solutions. Keeping software up-to-date and monitoring for vulnerabilities can prevent security lapses and ensure that systems remain resilient against emerging threats. Regularly reviewing and updating security policies, as well as conducting penetration testing, can identify potential weaknesses and improve overall cybersecurity resilience.
Compliance Considerations for Electronic Signatures
Compliance with legal and regulatory standards is a critical aspect of implementing electronic signatures. Different regions have specific requirements that organizations must adhere to, such as the eIDAS Regulation in the EU and the ESIGN Act in the US. Non-compliance can result in legal penalties and compromise the validity of signed documents.
Understanding Regulatory Requirements
Understanding the regulatory landscape is essential for IT and cybersecurity professionals. The Deloitte's guide on regulatory compliance for electronic signatures provides a comprehensive overview of these requirements and how to meet them.
In addition to legal compliance, industry-specific standards may also apply. For instance, the healthcare sector must consider HIPAA regulations when implementing electronic signatures, ensuring that patient information remains secure and confidential. Similarly, financial institutions must adhere to specific guidelines to protect client data and maintain transaction integrity.
Pro Tip: Engaging Legal and Compliance Experts
To navigate the complex landscape of compliance, consider engaging legal and compliance experts who can offer guidance and support. These professionals can help ensure that your electronic signature processes align with all relevant legal requirements and industry standards, minimizing the risk of non-compliance.
Future Trends in Electronic Signature Security
As technology continues to evolve, so too do the capabilities of electronic signatures. Emerging trends in this area are set to further enhance security and usability, offering new opportunities for IT and cybersecurity professionals to leverage these solutions.
AI and Machine Learning Integration
One significant trend is the integration of artificial intelligence (AI) and machine learning (ML) into electronic signature platforms. These technologies can enhance threat detection and automate compliance checks, reducing the burden on IT teams. MIT Technology Review's article on AI in electronic signatures explores these advancements in detail. AI can analyze patterns in signature usage to detect anomalies and potential security breaches, while ML can continuously learn and adapt to new threats.
Blockchain Enhancements
Another trend is the adoption of blockchain technology to provide immutable records of electronic transactions. This innovation not only enhances security but also offers transparency and traceability, making it easier to identify and address any discrepancies. Blockchain's decentralized nature ensures that records are tamper-proof, providing an additional layer of security to electronic signature processes.
Pro Tip: Stay Informed and Proactive
Staying ahead of these trends allows organizations to adopt cutting-edge solutions that enhance their data security measures and ensure the continued protection of sensitive information. Regularly attending industry conferences, subscribing to technology journals, and participating in online forums can keep you informed about the latest advancements in electronic signature security.
Expert Insights: Maximizing Security with Electronic Signatures
Industry experts emphasize the importance of a holistic approach to maximizing security with electronic signatures. This involves integrating these solutions into a broader cybersecurity strategy that encompasses all aspects of digital interactions.
Incorporating Electronic Signatures into a Holistic Security Framework
According to CSO Online's insights on holistic cybersecurity strategies, organizations that view electronic signatures as part of their overall security framework see a 50% reduction in data breach incidents. This underscores the effectiveness of incorporating electronic signatures into a comprehensive security model that includes encryption, access controls, and regular security audits.
Continuous Monitoring and Improvement
Experts also highlight the importance of continuous monitoring and regular updates to electronic signature solutions. Keeping software up-to-date and monitoring for vulnerabilities can prevent security lapses and ensure that systems remain resilient against emerging threats. Regularly reviewing and updating security policies, as well as conducting penetration testing, can identify potential weaknesses and improve overall cybersecurity resilience.
Pro Tip: Engage with Industry Experts
Engaging with industry experts and consultants can provide valuable insights and recommendations tailored to your organization's specific needs. These professionals can offer advice on best practices, emerging trends, and innovative solutions to enhance your electronic signature security.
FAQ: Common Questions About Electronic Signature Security
As electronic signatures become more prevalent, professionals often have questions about their security implications and best practices. Here, we address some of the most common inquiries to provide clarity and guidance.
1. Are electronic signatures legally binding?
Yes, electronic signatures are legally binding in most jurisdictions, provided they meet specific criteria outlined in regulations like the eIDAS Regulation and the ESIGN Act. These criteria ensure that electronic signatures are valid and enforceable. To meet these criteria, the signature must be uniquely linked to the signatory, capable of identifying the signatory, and created using means that the signatory can maintain under their sole control.
2. How do electronic signatures enhance data security?
Electronic signatures enhance data security by incorporating encryption, authentication, and audit trails. These features protect the integrity of signed documents and verify the identity of signatories, reducing the risk of unauthorized access. By using advanced encryption algorithms, electronic signatures ensure that data remains confidential and secure throughout the transaction process.
3. What are the common risks associated with electronic signatures?
Common risks include phishing attacks, fraudulent signatures, and non-compliance with regulatory standards. Implementing advanced security measures and staying informed about compliance requirements can mitigate these risks. Organizations should conduct regular security assessments to identify vulnerabilities and implement appropriate safeguards.
4. How can organizations ensure compliance with electronic signature regulations?
Organizations can ensure compliance by understanding relevant regulations, selecting solutions that meet these requirements, and regularly monitoring their electronic signature processes for adherence to legal standards. Engaging with legal experts and compliance officers can provide additional guidance and support in navigating complex regulatory environments.
5. What future developments can we expect in electronic signature technology?
Future developments include the integration of AI and blockchain technology, which will enhance security, automation, and transparency in electronic signature processes. Staying informed about these trends allows organizations to adopt advanced solutions proactively. As these technologies mature, they will offer new capabilities for detecting and mitigating threats, ensuring that electronic signature platforms remain at the forefront of digital security.
Conclusion: The Path Forward with Electronic Signatures
As organizations continue to navigate the digital landscape, electronic signatures offer a valuable tool for enhancing data security and compliance. By understanding their security features, implementing best practices, and staying informed about future trends, IT and cybersecurity professionals can effectively leverage electronic signatures to protect sensitive information.
For those looking to integrate electronic signatures into their workflows, consider exploring platforms like Zignature that offer robust security features and seamless integration capabilities. Additionally, enhancing your workflow automation with Apparatuz or streamlining recruitment processes with Applicantz can further optimize your business operations.
By adopting these strategies and solutions, organizations can maximize their data security efforts and maintain the integrity of their digital transactions in an ever-evolving cyber landscape.